Originally published at: Production ready End-to-End encryption and new user interfaces arrive with new Nextcloud clients - Nextcloud
 We’re very excited to announce the availability of version 3.0 of our desktop client and 3.13 for Android! With these releases come big improvements to the user interface, making it easier for users to access the apps in Nextcloud Hub. This releases introduce production-ready end-to-end encryption in our desktop and mobile clients.
We’re very excited to announce the availability of version 3.0 of our desktop client and 3.13 for Android! With these releases come big improvements to the user interface, making it easier for users to access the apps in Nextcloud Hub. This releases introduce production-ready end-to-end encryption in our desktop and mobile clients.
Earlier this year, Nextcloud Hub delivered a new generation of collaboration technology to the on-premises cloud market. With the release today, we bring more of this experience to the desktop client while adding the long-anticipated end-to-end encryption feature.
— Frank Karlitschek, CEO of Nextcloud GmbH
Production-ready end-to-end encryption
For most users, Nextcloud acts as a trusted, central repository of their most important data. Calendars, mails, documents, photos, chats and tasks, but also passwords, bookmarks and much more reside on a server you trust.
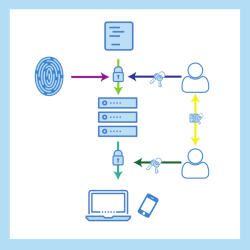
For a sub-set of extremely sensitive data, things like your social security number, passport and such, Nextcloud now introduces end-to-end encryption. The Nextcloud end-to-end encryption feature is designed such that the server never has access to unencrypted files or keys, nor does server-provided code ever handle unencrypted data which could provide avenues for compromise. You pick one or a few folders and encrypt them locally on the client, thus protecting them from any breach that might occur on the server.
As these files are no longer available on the server, and thus can not be shared with a public link, accessed in the browser or shared in a chat session, end-to-end encryption is not meant for the majority of data. Instead, it is meant to provide extra protection for your most sensitive information.
This per-folder capability available in the desktop and mobile clients encrypts all files as well as their names and metadata. Files will still be synced between the clients, but are not accessible online. Advanced key handling with Cryptographic Identity Protection in the form of server signed certificates facilitates the easy addition of new devices.
There is no need for user interaction or extra work and key sharing is seamlessly handled by the server, facilitating completely intuitive syncing. Only when adding a new device will you need to enter a passphrase, a mnemonic that your client can show you on demand.
In a future release, the scheme will allow for secure, end-to-end encrypted sharing with other users. Nextcloud supports an optional offline administrator recovery key and allows a complete audit log. The encryption design allows optionally for the deployment of a secure HSM to issue certificates to users in enterprises.
Organizations that demand the utmost security need a true enterprise solution that doesn’t require users to manually exchange encryption keys and long, complex passwords or share large, encrypted volumes. Nextcloud is first to market with an integrated, secure technology to keep a subset of highly sensitive files cryptographically secure even in the worst case of an undetected, full server breach.
— Roeland Douma, Security lead at Nextcloud
You can learn more about encryption in Nextcloud here and about end-to-end encryption here.
note: If you used the end-to-end encryption during our testing phase, in some cases your system has malformed keys installed which can break the syncing. Please follow the cleanup-steps from this forum thread if this happens to you!
note #2: As of Feb 2021, we are aware of some issues with E2EE that cause heavy server load and locking sync. Fixes are expected with the upcoming 3.2 release, most will also be backported to the 3.1.3 and 3.1.4 bugfix releases.
A new interface for the Desktop Client
Nextcloud Hub integrated our video chat app Talk, our groupware apps and an online office as standard components of Nextcloud. This release of the desktop client brings a number of important changes that make it easier and faster to access these other apps from the desktop.
The new menu for the desktop client makes Talk and other apps on the Nextcloud server quick to open. A click on the icon in the system tray pops up the new menu, showing a list of events on the server with on top user account information, a link to Files, Talk and a button that brings a list of other apps. From the list of server activity, you can even directly access the sharing settings of a file.
The menu makes it much easier and faster to access your apps, follow conversations or see what is happening with your files.
In the file manager, a right-click on a document now gives the option to edit directly in the online office document editor in Nextcloud. This makes it much quicker and easier to start editing files with others!
We also added the ability to add a note for the recipient of a file share in the share dialog.
Also a new interface for the Android client
With over 300 issues closed and pull requests merged, version 3.13 of the Android Nextcloud brings more than support for end-to-end encryption. This release also brings improvements to dark mode as well as a rewritten interface to fit the new Android design guidelines, adding a floating search bar on top with direct access to the users’ profile and the ability to switch between them. Below that are sort and list/icon view switchers, making the new interface fresh, clean and efficient.
The Android, iOS and desktop clients are all available via our download page.





