Support intro
Sorry to hear you’re facing problems ![]()
help.nextcloud.com is for home/non-enterprise users. If you’re running a business, paid support can be accessed via portal.nextcloud.com where we can ensure your business keeps running smoothly.
In order to help you as quickly as possible, before clicking Create Topic please provide as much of the below as you can. Feel free to use a pastebin service for logs, otherwise either indent short log examples with four spaces:
example
Or for longer, use three backticks above and below the code snippet:
longer
example
here
Some or all of the below information will be requested if it isn’t supplied; for fastest response please provide as much as you can ![]()
Nextcloud version (eg, 20.0.5): latest from linode marketplace
Operating system and version (eg, Ubuntu 20.04): Ubuntu 20.04
Apache or nginx version (eg, Apache 2.4.25): latest from linode marketplace
PHP version (eg, 7.4): latest from linode marketplace
The issue you are facing:
Randomly my Nextcloud was down and a reboot of the server and the Containers didnt fix it. made update some days ago. Reloading my linode backup litteraly results in a nextcloud with a working aio interface and the containers start, but the website in the end just returns a HTTP 502.
For testing i also just created a new linode with the Nextcloud AIO provided on the Marketplace and I get the exact same problem.
Is this the first time you’ve seen this error? (Y/N): Y
Steps to replicate it:
- Create new Linode with Nextcloud AIO
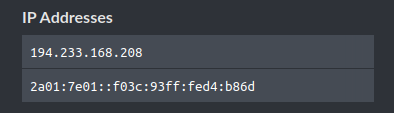
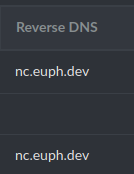
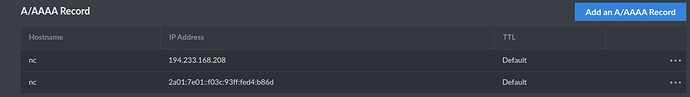
- Link your Domain again (yes ive changed the A, AAAA and the reverse DNS records)
- start Containers up
- get HTTP 502. when trying to visit
All logs are from the brand new Nextcloud Instance
The output of your Nextcloud log in Admin > Logging:
Trying to fix docker.sock permissions internally...
Creating docker group internally with id 999
Generating a RSA private key
.............................................................................................................................................................++++
....................................................................++++
writing new private key to './ssl.key'
-----
e[0;92mInitial startup of Nextcloud All In One complete!
You should be able to open the Nextcloud AIO Interface now on port 8080 of this server!
E.g. https://internal.ip.of.this.server:8080
If your server has port 80 and 8443 open and you point a domain to your server, you can get a valid certificate automatically by opening the Nextcloud AIO Interface via:
https://your-domain-that-points-to-this-server.tld:8443e[0m
{"level":"info","ts":1670184625.9491947,"msg":"using provided configuration","config_file":"/Caddyfile","config_adapter":""}
{"level":"warn","ts":1670184625.9518142,"msg":"Caddyfile input is not formatted; run the 'caddy fmt' command to fix inconsistencies","adapter":"caddyfile","file":"/Caddyfile","line":2}
{"level":"info","ts":1670184625.9542396,"logger":"admin","msg":"admin endpoint started","address":"localhost:2019","enforce_origin":false,"origins":["//[::1]:2019","//127.0.0.1:2019","//localhost:2019"]}
{"level":"info","ts":1670184625.9553556,"logger":"tls.cache.maintenance","msg":"started background certificate maintenance","cache":"0xc0004efce0"}
{"level":"warn","ts":1670184625.955654,"logger":"http","msg":"server is listening only on the HTTP port, so no automatic HTTPS will be applied to this server","server_name":"srv0","http_port":80}
{"level":"warn","ts":1670184625.9565105,"logger":"http","msg":"automatic HTTP->HTTPS redirects are disabled","server_name":"srv1"}
{"level":"warn","ts":1670184625.9571204,"logger":"tls","msg":"YOUR SERVER MAY BE VULNERABLE TO ABUSE: on-demand TLS is enabled, but no protections are in place","docs":"https://caddyserver.com/docs/automatic-https#on-demand-tls"}
{"level":"info","ts":1670184625.9575257,"logger":"tls","msg":"cleaning storage unit","description":"FileStorage:/mnt/docker-aio-config/caddy/"}
{"level":"info","ts":1670184625.9575632,"logger":"tls","msg":"finished cleaning storage units"}
{"level":"info","ts":1670184625.9584646,"logger":"http.log","msg":"server running","name":"srv0","protocols":["h1","h2","h3"]}
{"level":"info","ts":1670184625.9588099,"logger":"http","msg":"enabling HTTP/3 listener","addr":":8443"}
{"level":"info","ts":1670184625.9604893,"msg":"failed to sufficiently increase receive buffer size (was: 208 kiB, wanted: 2048 kiB, got: 416 kiB). See https://github.com/lucas-clemente/quic-go/wiki/UDP-Receive-Buffer-Size for details."}
{"level":"info","ts":1670184625.9608552,"logger":"http.log","msg":"server running","name":"srv1","protocols":["h1","h2","h3"]}
{"level":"error","ts":1670184625.9612865,"msg":"unable to create folder for config autosave","dir":"/root/.config/caddy","error":"mkdir /root/.config: permission denied"}
{"level":"info","ts":1670184625.9615667,"msg":"serving initial configuration"}
AH00558: apache2: Could not reliably determine the server's fully qualified domain name, using 172.17.0.2. Set the 'ServerName' directive globally to suppress this message
[Sun Dec 04 20:10:26.027282 2022] [ssl:warn] [pid 103] AH01906: 172.17.0.2:8080:0 server certificate is a CA certificate (BasicConstraints: CA == TRUE !?)
[Sun Dec 04 20:10:26.027605 2022] [ssl:warn] [pid 103] AH01909: 172.17.0.2:8080:0 server certificate does NOT include an ID which matches the server name
AH00558: apache2: Could not reliably determine the server's fully qualified domain name, using 172.17.0.2. Set the 'ServerName' directive globally to suppress this message
[Sun Dec 04 20:10:26.062745 2022] [ssl:warn] [pid 103] AH01906: 172.17.0.2:8080:0 server certificate is a CA certificate (BasicConstraints: CA == TRUE !?)
[Sun Dec 04 20:10:26.063193 2022] [ssl:warn] [pid 103] AH01909: 172.17.0.2:8080:0 server certificate does NOT include an ID which matches the server name
[Sun Dec 04 20:10:26.068807 2022] [mpm_prefork:notice] [pid 103] AH00163: Apache/2.4.54 (Debian) PHP/8.0.25 OpenSSL/1.1.1n configured -- resuming normal operations
[Sun Dec 04 20:10:26.069170 2022] [core:notice] [pid 103] AH00094: Command line: 'apache2 -D FOREGROUND'
Deleting duplicate sessions
{"level":"info","ts":1670185047.7668793,"logger":"tls.on_demand","msg":"obtaining new certificate","remote_ip":"172.17.0.1","remote_port":"60780","server_name":"nc.euph.dev"}
{"level":"info","ts":1670185047.7743065,"logger":"tls.obtain","msg":"acquiring lock","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185047.7847872,"logger":"tls.obtain","msg":"lock acquired","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185047.785931,"logger":"tls.obtain","msg":"obtaining certificate","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185048.6442845,"logger":"http","msg":"waiting on internal rate limiter","identifiers":["nc.euph.dev"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1670185048.6443753,"logger":"http","msg":"done waiting on internal rate limiter","identifiers":["nc.euph.dev"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1670185049.068219,"logger":"http.acme_client","msg":"trying to solve challenge","identifier":"nc.euph.dev","challenge_type":"tls-alpn-01","ca":"https://acme-v02.api.letsencrypt.org/directory"}
{"level":"error","ts":1670185049.6181734,"logger":"http.acme_client","msg":"challenge failed","identifier":"nc.euph.dev","challenge_type":"tls-alpn-01","problem":{"type":"urn:ietf:params:acme:error:tls","title":"","detail":"2a01:7e01::f03c:93ff:fe41:4556: remote error: tls: internal error","instance":"","subproblems":[]}}
{"level":"error","ts":1670185049.6190717,"logger":"http.acme_client","msg":"validating authorization","identifier":"nc.euph.dev","problem":{"type":"urn:ietf:params:acme:error:tls","title":"","detail":"2a01:7e01::f03c:93ff:fe41:4556: remote error: tls: internal error","instance":"","subproblems":[]},"order":"https://acme-v02.api.letsencrypt.org/acme/order/855929877/150356750797","attempt":1,"max_attempts":3}
{"level":"info","ts":1670185051.183939,"logger":"http.acme_client","msg":"trying to solve challenge","identifier":"nc.euph.dev","challenge_type":"http-01","ca":"https://acme-v02.api.letsencrypt.org/directory"}
{"level":"info","ts":1670185051.5204847,"logger":"http","msg":"served key authentication","identifier":"nc.euph.dev","challenge":"http-01","remote":"172.17.0.1:37640","distributed":false}
{"level":"info","ts":1670185051.5784826,"logger":"http","msg":"served key authentication","identifier":"nc.euph.dev","challenge":"http-01","remote":"172.17.0.1:37648","distributed":false}
{"level":"info","ts":1670185051.5887218,"logger":"http","msg":"served key authentication","identifier":"nc.euph.dev","challenge":"http-01","remote":"172.17.0.1:37660","distributed":false}
{"level":"info","ts":1670185052.0842876,"logger":"http.acme_client","msg":"authorization finalized","identifier":"nc.euph.dev","authz_status":"valid"}
{"level":"info","ts":1670185052.0843225,"logger":"http.acme_client","msg":"validations succeeded; finalizing order","order":"https://acme-v02.api.letsencrypt.org/acme/order/855929877/150356756727"}
{"level":"info","ts":1670185053.5916781,"logger":"http.acme_client","msg":"successfully downloaded available certificate chains","count":2,"first_url":"https://acme-v02.api.letsencrypt.org/acme/cert/04056684055a07a9acca3f4ab2650844a7f8"}
{"level":"info","ts":1670185053.5923557,"logger":"tls.obtain","msg":"certificate obtained successfully","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185053.592418,"logger":"tls.obtain","msg":"releasing lock","identifier":"nc.euph.dev"}
c 04 20:17:37.269965 2022] [php:notice] [pid 826] [client 127.0.0.1:53750] 404 Not Found\nType: Slim\\Exception\\HttpNotFoundException\nCode: 404\nMessage: Not found.\nFile: /var/www/docker-aio/php/vendor/slim/slim/Slim/Middleware/RoutingMiddleware.php\nLine: 76\nTrace: #0 /var/www/docker-aio/php/vendor/slim/slim/Slim/Routing/RouteRunner.php(56): Slim\\Middleware\\RoutingMiddleware->performRouting(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#1 /var/www/docker-aio/php/vendor/slim/csrf/src/Guard.php(476): Slim\\Routing\\RouteRunner->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#2 /var/www/docker-aio/php/vendor/slim/slim/Slim/MiddlewareDispatcher.php(168): Slim\\Csrf\\Guard->process(Object(GuzzleHttp\\Psr7\\ServerRequest), Object(Slim\\Routing\\RouteRunner))\n#3 /var/www/docker-aio/php/vendor/slim/twig-view/src/TwigMiddleware.php(115): Psr\\Http\\Server\\RequestHandlerInterface@anonymous->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#4 /var/www/docker-aio/php/vendor/slim/slim/Slim/MiddlewareDispatcher.php(121): Slim\\Views\\TwigMiddleware->process(Object(GuzzleHttp\\Psr7\\ServerRequest), Object(Psr\\Http\\Server\\RequestHandlerInterface@anonymous))\n#5 /var/www/docker-aio/php/src/Middleware/AuthMiddleware.php(38): Psr\\Http\\Server\\RequestHandlerInterface@anonymous->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#6 /var/www/docker-aio/php/vendor/slim/slim/Slim/MiddlewareDispatcher.php(269): AIO\\Middleware\\AuthMiddleware->__invoke(Object(GuzzleHttp\\Psr7\\ServerRequest), Object(Psr\\Http\\Server\\RequestHandlerInterface@anonymous))\n#7 /var/www/docker-aio/php/vendor/slim/slim/Slim/Middleware/ErrorMiddleware.php(76): Psr\\Http\\Server\\RequestHandlerInterface@anonymous->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#8 /var/www/docker-aio/php/vendor/slim/slim/Slim/MiddlewareDispatcher.php(121): Slim\\Middleware\\ErrorMiddleware->process(Object(GuzzleHttp\\Psr7\\ServerRequest), Object(Psr\\Http\\Server\\RequestHandlerInterface@anonymous))\n#9 /var/www/docker-aio/php/vendor/slim/slim/Slim/MiddlewareDispatcher.php(65): Psr\\Http\\Server\\RequestHandlerInterface@anonymous->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#10 /var/www/docker-aio/php/vendor/slim/slim/Slim/App.php(199): Slim\\MiddlewareDispatcher->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#11 /var/www/docker-aio/php/vendor/slim/slim/Slim/App.php(183): Slim\\App->handle(Object(GuzzleHttp\\Psr7\\ServerRequest))\n#12 /var/www/docker-aio/php/public/index.php(167): Slim\\App->run()\n#13 {main}, referer: https://194.233.163.54:8080/api/docker/logs?id=nextcloud-aio-nextcloud
heres the log of the appache container
nc: getaddrinfo for host "nextcloud-aio-nextcloud" port 9000: Name or service not known
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
AH00558: apache2: Could not reliably determine the server's fully qualified domain name, using 172.17.0.8. Set the 'ServerName' directive globally to suppress this message
{"level":"info","ts":1670185020.606288,"msg":"using provided configuration","config_file":"/Caddyfile","config_adapter":""}
{"level":"warn","ts":1670185020.6089551,"msg":"Caddyfile input is not formatted; run the 'caddy fmt' command to fix inconsistencies","adapter":"caddyfile","file":"/Caddyfile","line":2}
{"level":"info","ts":1670185020.610524,"logger":"admin","msg":"admin endpoint started","address":"localhost:2019","enforce_origin":false,"origins":["//localhost:2019","//[::1]:2019","//127.0.0.1:2019"]}
{"level":"info","ts":1670185020.611196,"logger":"http","msg":"server is listening only on the HTTPS port but has no TLS connection policies; adding one to enable TLS","server_name":"srv0","https_port":443}
{"level":"warn","ts":1670185020.6112387,"logger":"http","msg":"automatic HTTP->HTTPS redirects are disabled","server_name":"srv0"}
{"level":"info","ts":1670185020.6116002,"logger":"tls.cache.maintenance","msg":"started background certificate maintenance","cache":"0xc000235b20"}
{"level":"info","ts":1670185020.613386,"logger":"tls","msg":"cleaning storage unit","description":"FileStorage:/mnt/data/caddy"}
{"level":"info","ts":1670185020.613428,"logger":"tls","msg":"finished cleaning storage units"}
{"level":"info","ts":1670185020.6137416,"logger":"http","msg":"enabling HTTP/3 listener","addr":":443"}
{"level":"info","ts":1670185020.6140435,"msg":"failed to sufficiently increase receive buffer size (was: 208 kiB, wanted: 2048 kiB, got: 416 kiB). See https://github.com/lucas-clemente/quic-go/wiki/UDP-Receive-Buffer-Size for details."}
{"level":"info","ts":1670185020.6144648,"logger":"http.log","msg":"server running","name":"srv0","protocols":["h1","h2","h3"]}
{"level":"info","ts":1670185020.6148458,"logger":"http","msg":"enabling automatic TLS certificate management","domains":["nc.euph.dev"]}
{"level":"info","ts":1670185020.6154604,"logger":"tls.obtain","msg":"acquiring lock","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185020.6160269,"msg":"autosaved config (load with --resume flag)","file":"/var/www/.config/caddy/autosave.json"}
{"level":"info","ts":1670185020.6163936,"msg":"serving initial configuration"}
{"level":"info","ts":1670185020.6173255,"logger":"tls.obtain","msg":"lock acquired","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185020.6174133,"logger":"tls.obtain","msg":"obtaining certificate","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185021.3523228,"logger":"http","msg":"waiting on internal rate limiter","identifiers":["nc.euph.dev"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1670185021.3523927,"logger":"http","msg":"done waiting on internal rate limiter","identifiers":["nc.euph.dev"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1670185021.7712326,"logger":"http.acme_client","msg":"trying to solve challenge","identifier":"nc.euph.dev","challenge_type":"tls-alpn-01","ca":"https://acme-v02.api.letsencrypt.org/directory"}
{"level":"info","ts":1670185022.179047,"logger":"tls","msg":"served key authentication certificate","server_name":"nc.euph.dev","challenge":"tls-alpn-01","remote":"172.17.0.1:57452","distributed":false}
{"level":"info","ts":1670185022.2054675,"logger":"tls","msg":"served key authentication certificate","server_name":"nc.euph.dev","challenge":"tls-alpn-01","remote":"172.17.0.1:57458","distributed":false}
{"level":"info","ts":1670185022.4415376,"logger":"tls","msg":"served key authentication certificate","server_name":"nc.euph.dev","challenge":"tls-alpn-01","remote":"172.17.0.1:57462","distributed":false}
{"level":"info","ts":1670185022.7029483,"logger":"http.acme_client","msg":"authorization finalized","identifier":"nc.euph.dev","authz_status":"valid"}
{"level":"info","ts":1670185022.7033584,"logger":"http.acme_client","msg":"validations succeeded; finalizing order","order":"https://acme-v02.api.letsencrypt.org/acme/order/855929587/150356637697"}
{"level":"info","ts":1670185024.2394726,"logger":"http.acme_client","msg":"successfully downloaded available certificate chains","count":2,"first_url":"https://acme-v02.api.letsencrypt.org/acme/cert/04795175c8605e696540850ce1858ad47db9"}
{"level":"info","ts":1670185024.2404716,"logger":"tls.obtain","msg":"certificate obtained successfully","identifier":"nc.euph.dev"}
{"level":"info","ts":1670185024.2405465,"logger":"tls.obtain","msg":"releasing lock","identifier":"nc.euph.dev"}
{"level":"error","ts":1670185049.3893533,"logger":"tls","msg":"tls-alpn challenge","server_name":"nc.euph.dev","error":"no information found to solve challenge for identifier: nc.euph.dev"}
{"level":"error","ts":1670185049.5240107,"logger":"tls","msg":"tls-alpn challenge","server_name":"nc.euph.dev","error":"no information found to solve challenge for identifier: nc.euph.dev"}