Debian 11 Stable on a x64 NUC
Nextcloud 24.0.5.1
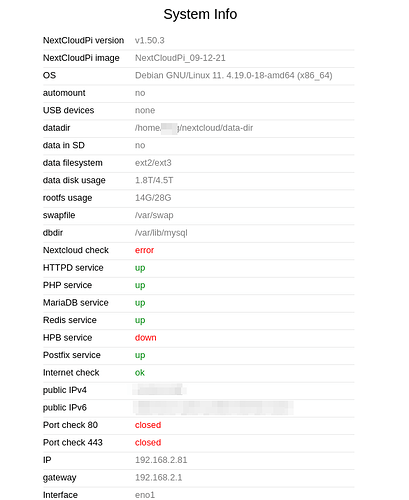
NextCloudPi version v1.50.3
PHP 7.4.30
Major issue, PHP 8.1
Oct. 22nd I ran a package update on my Debian 11 server and it updated the PHP version to 8.1x. After this I was unable to access the webUI for Nextcloud, and Webdav wouldn’t communicate. I rolled it back with a snapshot to undo the package updates, and it all works again. I read here [SOLVED] After Debian 11 upgrade "Failed to connect to the database..." that Nextcloud doesn’t support PHP8.1 yet. If this is true and the only solution is to not use that version, how can I hold this back to prevent issues?
This was my output for the package upgrades/updates in Debian:
Install: php8.1-opcache:amd64 (8.1.11-1+0~20220929.27+debian11~1.gbpe414ce, automatic), php8.1-common:amd64 (8.1.11-1+0~20220929.27+debian11~1.gbpe414ce, automatic), php8.1-readline:amd64 (8.1.11-1+0~20220929.27+debian11~1.gbpe414ce, automatic), php8.1-igbinary:amd64 (3.2.6+2.0.8-6+0~20220131.33+debian11~1.gbp1d540e, automatic), php8.1-phpdbg:amd64 (8.1.11-1+0~20220929.27+debian11~1.gbpe414ce, automatic), php8.1-redis:amd64 (5.3.7+4.3.0-1+0~20220330.42+debian11~1.gbp6fe8b7, automatic), php8.1-cli:amd64 (8.1.11-1+0~20220929.27+debian11~1.gbpe414ce, automatic)
Upgrade: php7.4-mbstring:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), libc6-i386:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), php-redis:amd64 (5.3.2+4.3.0-2+deb11u1, 5.3.7+4.3.0-1+0~20220330.42+debian11~1.gbp6fe8b7), php7.4-readline:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-gd:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-curl:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), tzdata:amd64 (2021a-1+deb11u5, 2021a-1+deb11u7), libpcre3:amd64 (2:8.39-13, 2:8.44-2+0~20210301.9+debian11~1.gbpa278ad), php7.4-bcmath:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-intl:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-opcache:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php-common:amd64 (2:76, 2:92+0~20220117.43+debian11~1.gbpe0d14e), php7.4:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-bz2:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-cli:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-mysql:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-fpm:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-gmp:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), libxml2:amd64 (2.9.10+dfsg-6.7+deb11u2, 2.9.14+dfsg-0+0~20220524.12+debian11~1.gbpc5dc45), php7.4-json:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php-igbinary:amd64 (3.2.1+2.0.8-2, 3.2.6+2.0.8-6+0~20220131.33+debian11~1.gbp1d540e), php7.4-xml:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-zip:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), libc6:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), locales:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), libpcre2-16-0:amd64 (10.36-2+deb11u1, 10.40-1+0~20220713.16+debian11~1.gbpb6cec5), libpcre2-8-0:amd64 (10.36-2+deb11u1, 10.40-1+0~20220713.16+debian11~1.gbpb6cec5), php7.4-common:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), php7.4-ldap:amd64 (7.4.30-1+deb11u1, 1:7.4.32-1+0~20220929.71+debian11~1.gbpe9c007), libc-dev-bin:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), libc-l10n:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), grub-common:amd64 (2.06-3~deb11u1, 2.06-3~deb11u2), libc-bin:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), libc-devtools:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), libc6-dev:amd64 (2.31-13+deb11u4, 2.31-13+deb11u5), libgd3:amd64 (2.3.0-2, 2.3.3-5+0~20220711.9+debian11~1.gbp72b297)
Minor issue - NCP version update
- I ran NextcloudPi update and it updated to v1.50.3 and now the port status on the web panel server status shows closed for “port check 80” and “port check 443” as referenced here Open ports check fail due to an url change in ncp-diag file · Issue #1643 · nextcloud/nextcloudpi · GitHub this doesn’t seem to harm anything…
- more importantly, This version update also seems to have broken my ability to restore a backup. i wanted to restore a backup of an older version of NCP, it proceeded and looked complete, but at the end it states there was an error and to try refreshing the page. Not sure if it’s related to this? After updating to v1.50.1 HPB service shows "down", nextcloud unreachable · Issue #1593 · nextcloud/nextcloudpi · GitHub
Below is a screenshot of my system info before reverting the package updates to the older PHP version.
NextcloudPi log for that day Sat 22 Oct 2022 07:35:43 AM EDT - Running /etc/cron.daily/ncp-autoupdate...[ n - Pastebin.com
Could someone help me determine the root cause for both issues, and how to resolve it? My system works now, but not performing system updates isn’t a good solution.