Hello, first time poster (though I’ve been using nc for some years mostly as a calendar/contacts server).
I recently (finally!) got my Nextcloud setup on my home network on an older Raspberry Pi (I used to have it hosted on a virtual server) and because of literally days tearing my hair out trying to get my calendar setup on my MacBook and iPhone (and an Android phone) I thought I’d post my experiences and findings in case it helps someone else.
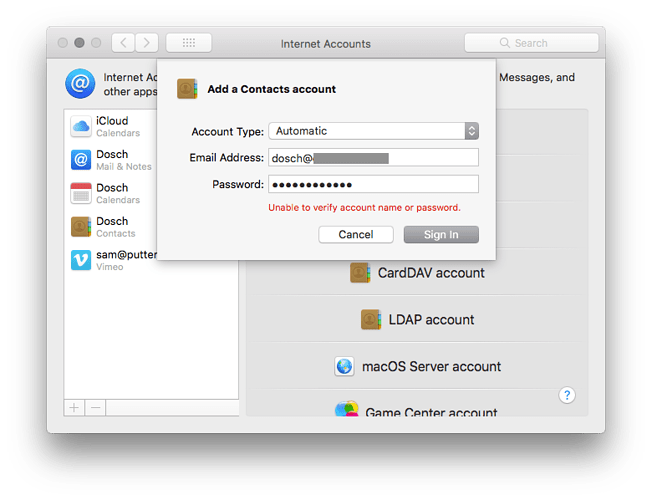
First off I have to say that most of my woes came from the really awful error reporting both on OS X Calendar and iOS Calendar. Your problem could be bad SSL setup, a mistake in the server URL…anything…and the error messages are either all the same (‘Cannot verify DAV’ or ‘Cannot connect via SSL’… I’m sure you’ve seen them) or just non-existent. This is very, very poor on Apple’s part (and I’m what can be considered one of those awful ‘fan boys’ of Apple generally…)
Having said that, most guides or how-tos on how to get your Nextcloud calendar set up are either incorrect or incomplete it would seem.
Here’s my findings with the caveat that you Nextcloud installation is beind HTTPS and that’s set up and working properly. I’m not about to go into detail on that as I’m still raw and smarting from having to self-learn that stuff (mostly by trial and error!). With that in mind too, I may have some of the SSL/HTTPS stuff wrong (for example I’m only using a self certificate generated by openssl as described in this guide (which is one of the better ones I found for actually getting Nextcloud up and running on a Pi by the way…):
https://pimylifeup.com/raspberry-pi-nextcloud-server/
MacBook, OSX Catalina, Apple Calendar app:
The biggest problem I had here was with SSL. It seems that the Calendar app can’t cope with self-certified servers. I won’t get into an argument about the dangers or non-compliance of running with a self-certified setup here, that’s not the point of this post. The problem is, Calendar doesn’t tell you this, it just fails without a useful error. I did manage to find a fairly reliable workaround though.
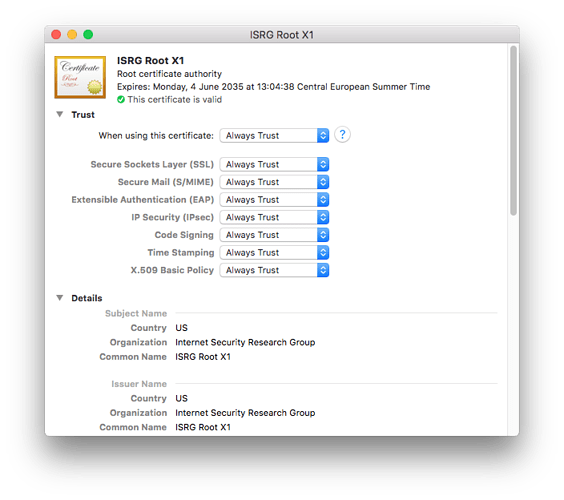
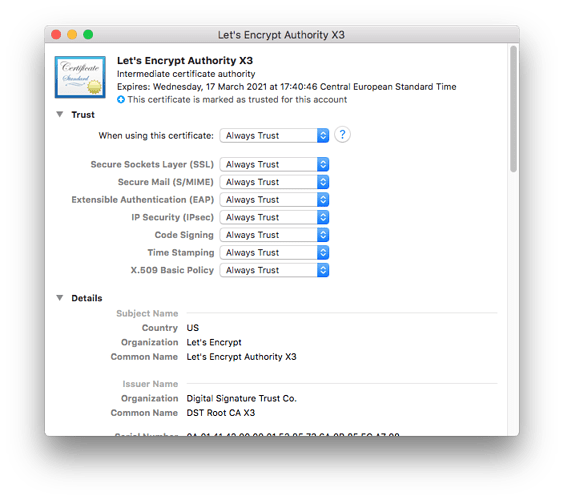
- Clear out any certificates linked to the IP/URL of your nextcloud server from Keychain Access.
- Using only Safari browser, navigate to the (https) URL of your nextcloud installation.
- You will get an error telling you it’s unsafe. Proceed to open the website anyway (I can’t remember the exact details) and it should ask you for your password as you are changing your trust certificates (or something similar).
- Once your NC site has opened in Safari, you should have a new certificate intalled in your Keychain.
It would seem that only Safari installs system-wide certificates. This is necessary becasue there is no way to add/accept a self-certified certificate in Calendar. OK, onto Calendar:
-
Open Calendar and then go to Add Account
-
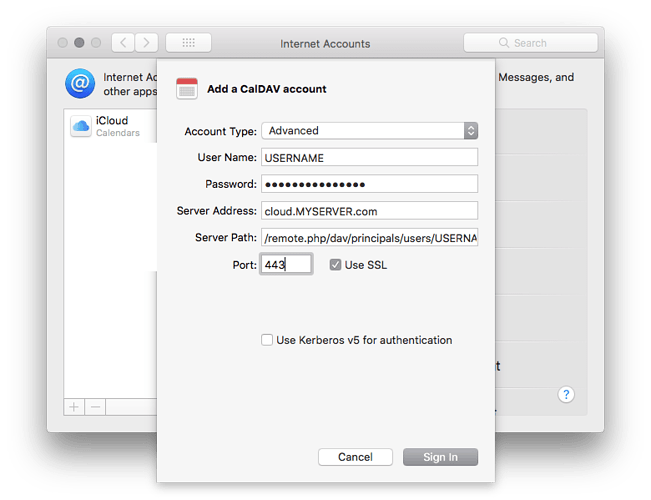
Choose Other/CalDAV
-
Choose the Advanced option
-
Enter the following:
Username: --your NC username–
Password: --your NC password–
Server Address: yournextcloudserver.com (or .net or whatever)*
Server Path: /nextcloud/remote.php/dav/principals/users/yourusername
Port: 443 (or whatever port it is behind, 443 is default SSL)
Use SSL: YES
Use Kerberos: NO
- just use the bare name, don’t prefix it with https:// or add any port numbers
This should work. It’s the most consistent method I came up with.
iPhone 7, iOS 15
Unfortunately this is by far the most awful setup to get right. The main issue here is that it’s just not possible (for a general user) to remove a trust certificate that has been manually installed on your phone in the way you would in Safari as per the desktop instructions above. Apparently there is an Apple Phone Management tool that is meant for use by enterprise or education IT managers for managing a bunch of iPhones with group policies/payloads etc. This is the only way you can manage/delete trust certificates. I can’t verify this as I have no access to such a tool. One website comment I read said the only option to regular users, if you’re in a situation that there is a conflict/problem with the trust certificates on your phone (that was the problem for me), is to actually wipe your phone. Insane. I tried doing a ‘Reset Networking’ half-way measure a couple of times but I couldn’t scientifically say if this helped. I suspect it did.
Anyway, down to details:
- Settings, Calendar
- Add account, select Add CalDAV account
- Use these settings:
Server: https://yournextcloudserver.com:(*port numer)/nextcloud/remote.php/dav/principals/users/yourusername/
Username: --your NC username–
Password: --your NC password–
*port number: if think if your server is behind 443 then you don’t need to specify the port. Mine is behind a custom port number. If yours is too add the port number here.
What happens at this point may well depend on your setup. When I click ‘Next’ I get a trust/certificate warning and a dialogue with three choices, one of which is ‘Details’. This is the one you want. Click that and it will show you the certificate from your NC server. Tap on ‘Trust’ to accept and install it. You might have to click on Advanced Settings and turn on SSL and add the port number - 443 for standard SSL or whatever port number you’re using. I think you then tap ‘Save’ to proceed.
While this is not a clear and simple guide, I posted as much detail as I could remeber (and took note of!) so that it might be useful to anyone else struggling. Again, as I said, I think the core of the problem is Apple’s woeful handling of self-certified servers both in the desktop Calendar app and the iOS Calander app/add account dialogue. Of course the other caveat is that this might be different depending on the OSX/iOS version you’re running.
![]()