is somewhere explained how the security of this app is handeled? i’m looking for answers at: are the passwords stored encrypted, when will they be decrypted and how ?
The app allows the use of client side encryption and server side encryption.
By default, the app encrypts and decrypts passwords on the server and sends them unencrypted to the client. (so only server side encryption)
If you use a nightly version of the app, you can also use the client side encryption with libsodium in the browser, but it is not enabled by default since browser plugins and other apps still need to be adapted to it (https://github.com/marius-wieschollek/passwords/issues/80)
Good afternoon! I wanted to ask, considering the Passwords app description states that it uses Nextcloud’s integrated encryption functionality as stated:
Passwords offers a safe server side encryption using Nextclouds integrated encryption functionality. Each password is encrypted with it’s own unique key.
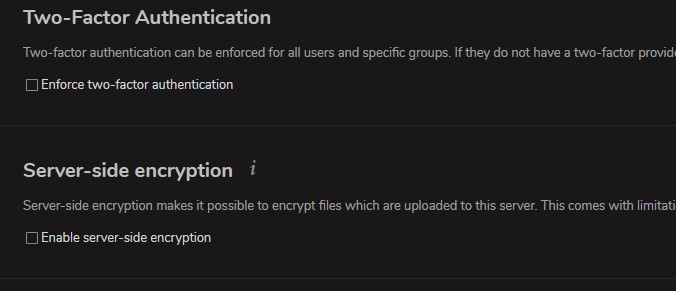
Are passwords safe regarding server side encryption if the “Server-side encryption” is not enabled in the security settings of Nextcloud.
I wanted to make sure I understood the security implications of this and if this option affects it or not. Probably a dumb question but I just wanted to make sure.
Thanks for helping me understand this!
The Server-side encryption option is only for files.
The app itself uses the encryption code that is provided by Nextcloud for apps. The encryption is always active regardless of any settings in the admin ui. You can see the encryption used for each password in the details of that password in the app.
The text in the readme is there to highlight that the app do not implement its own encryption. (Because implementing your own encryption is usually a bad idea)
Hi,
is there something new about client side encryption for the password app ?
Yes, the progress is documented in the github issue that is the selected answer
So, if I understand it right, there’s a little risk that the password could be intercepted on its way from the server to the browser of the user not being send encrypted, right? What do you think?
Thank you!
In case someone manages to intercept the traffic between the browser and the server, your entire setup is compromised and no longer trustworthy.
In this case the Passwords app - with or without the client side encryption - is insecure because the attacker could manipulate the source code sent to the browser and just steal the master password or the decrypted data.
The same is valid for any browser extension with the permission to access the content of a tab. It is also valid for any app you install in your Nextcloud. An evil or insecure (XSS) app can compromise any content in Nextcloud.
This is not only valid for the Passwords app, but for absolutely any web-based password manager. (and any browser for extensions)
The client side encryption will only be effective if used with external apps such as the browser extension. (This is also the reason why the Nextcloud E2E only works with the client)
So in short unless both are enabled on both the client and server sided the passwords are able to be comprised readily simply? If so why isn’t this the default in the “stock” NextCloud installation even? What the point then if the passwords are sent as clear text to and from the client and server housing the installation?
No. My point was that if someone manages to intercept traffic between the server and the browser - meaning someone breaks the HTTPS of your server - then no encryption offered by the app will be useful because the attacker can manipulate the source code of the app.
Because writing a client side encryption takes a lot of time. And just letting users set up the encryption in the app and then having them discover that they can’t use it with any other app right now won’t be very helpful.
Ok, let’s become more specific, because I also don’t understand whar you really mean with “browser extensions”. It’s quite simple: My nextcloud account is on a public server (not my own). So, normally it would be quite a simple option to store my passwords in the nextcloud app and use the one-click feature that copies the password to the clipboard to paste it in any application of a PC you want to have access to. So much for the theory. The question is now: When I copy the password into the clipboard, what happens? I imagine it’s send as clear text from the server to my PC to my clipboard, right? If this is right, it should be possible to compromise/intercept/read the password on its way through the net (to my PC/device), right? That’s the only thing that’s essential for me in this case for obvious reasons. Of course, it may be possible that the password is decrypted when it’s arrived on the PC. That’s what I would like to know …
Thank you
I imagine it’s send as clear text from the server to my PC to my clipboard, right?
No. Passwords are always sent to the browser encrypted with HTTPS.
In a normal situation only you can see your passwords, they are stored encrypted on the server and they are never sent over the internet as plain text.
My original answer was based on the assumption that you wanted to know what happens if someone manages to intercept the HTTPS encrypted traffic between your browser and the server.
If you want to know more about the different encryption methods offered by the app or if you want to know how an attacker could gain access to your passwords (and what you can do against that), you can check out the security page from the official wiki which will also be part of the user manual in the app once it is finished.
Ok, thank you very much! This makes sense and it’s for the present the most important thing for me. Just good to know that I don’t have to worry using this option as it’s quite simple and doesn’t require special software, setups, synchros and all this stuff … 

Hi, I read here, that the app is encrypting passwords. But how it is about other parts?
For example if the password is a file. I see here just an option to link to a file stored in the NC cloud.
That leads me to the point, that maybe beside the password nothing is encrypted.
Could someone help me to clear this?
The passwords app encrypts the data stored in the passwords app. So the passwords entries, folders and tags in the passwords app are encrypted.
Linked files are not stored in the passwords and are not encrypted by the app. But the information about the link that is stored with the password entry is encrypted by the passwords app. You should use one of the existing official apps if you want to encrypt files.
Thats pity. I do not want to encrypt the whole NC instance, which is btw. no help, if someone has access to the NC server.
End-to-end encryption needs < NC 20.0 and mine is running 21.
I just want to protect some private keys a bit more.
If NC do not provide this, I will maybe use a zip container or so.
The state of the E2EE app is really a shame for Nextcloud. The advertise it on their website, but the app seems to be buggy and abandonware.
You could try cryptomator.
Fortunately there is a new release of the E2EE app for NC21 just uploaded to the appstore (see this comment).
And as I heard, it runs meanwhile pretty stable on NC20 (and probably NC21, too).
I wish I had seen this post or there was some warning about compatibility before encryption could be enabled. I enabled client-side encryption only to find out that it’s not compatible with the Android app. Now I’m stuck without access to my passwords on mobile!! Is there any way to reverse and disable the password encryption from the browser, or do I have to basically delete everything and re-import my passwords again from LastPass?