Hey guys,
I just tried and installed the Docker AIO on my Synology and everything works fine, just the collabora/NextCloud Office is not working.
I tried to do everything from the debug discussion here:
/etc/hosts:
127.0.0.1 localhost
::1 localhost ip6-localhost ip6-loopback
fe00::0 ip6-localnet
ff00::0 ip6-mcastprefix
ff02::1 ip6-allnodes
ff02::2 ip6-allrouters
192.168.32.8 4abbc647afe4
Collabora logs:
wsd-00001-00035 2023-03-07 08:37:28.464419 +0100 [ prisoner_poll ] TRC #20: Pong received: 290 microseconds| net/WebSocketHandler.hpp:374
wsd-00001-00035 2023-03-07 08:37:28.464448 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:28.464455 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:28.464461 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 5000000 size 2| net/Socket.cpp:338
wsd-00001-00001 2023-03-07 08:37:31.180136 +0100 [ coolwsd ] INF Waiting for a new child for a max of 20000ms| wsd/COOLWSD.cpp:5507
wsd-00001-00035 2023-03-07 08:37:33.468037 +0100 [ prisoner_poll ] TRC Poll completed with 0 live polls max (5000000us)(timedout)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:33.468242 +0100 [ prisoner_poll ] TRC #20: Starting handling poll results of prisoner_poll at index 1 (of 2): 0| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:33.468254 +0100 [ prisoner_poll ] TRC #20: Revents: 0x0| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:33.468286 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:33.468295 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:33.468301 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 5000000 size 2| net/Socket.cpp:338
wsd-00001-00035 2023-03-07 08:37:38.472670 +0100 [ prisoner_poll ] TRC Poll completed with 0 live polls max (5000000us)(timedout)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:38.472762 +0100 [ prisoner_poll ] TRC #19: Starting handling poll results of prisoner_poll at index 0 (of 2): 0| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:38.472773 +0100 [ prisoner_poll ] TRC #20: Revents: 0x0| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:38.472785 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:38.472792 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:38.472797 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 5000000 size 2| net/Socket.cpp:338
wsd-00001-00035 2023-03-07 08:37:43.476459 +0100 [ prisoner_poll ] TRC Poll completed with 0 live polls max (5000000us)(timedout)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:43.476529 +0100 [ prisoner_poll ] TRC #20: Starting handling poll results of prisoner_poll at index 1 (of 2): 0| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:43.476538 +0100 [ prisoner_poll ] TRC #20: Revents: 0x0| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:43.476549 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:43.476556 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:43.476561 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 2987580 size 2| net/Socket.cpp:338
wsd-00001-00035 2023-03-07 08:37:46.465680 +0100 [ prisoner_poll ] TRC Poll completed with 0 live polls max (2987580us)(timedout)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:46.465751 +0100 [ prisoner_poll ] TRC #19: Starting handling poll results of prisoner_poll at index 0 (of 2): 0| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:46.465784 +0100 [ prisoner_poll ] TRC #20: Revents: 0x0| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:46.465794 +0100 [ prisoner_poll ] TRC #20: Sending ping.| net/WebSocketHandler.hpp:580
wsd-00001-00035 2023-03-07 08:37:46.465804 +0100 [ prisoner_poll ] TRC WebSocketHandler: Writing 1 bytes to #20 in addition to 0 bytes buffered| net/WebSocketHandler.hpp:761
wsd-00001-00035 2023-03-07 08:37:46.465835 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:46.465843 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x5| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:46.465872 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 5000000 size 2| net/Socket.cpp:338
wsd-00001-00035 2023-03-07 08:37:46.465882 +0100 [ prisoner_poll ] TRC Poll completed with 1 live polls max (5000000us)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:46.465890 +0100 [ prisoner_poll ] TRC #20: Starting handling poll results of prisoner_poll at index 1 (of 2): 4| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:46.465898 +0100 [ prisoner_poll ] TRC #20: Revents: 0x4| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:46.465924 +0100 [ prisoner_poll ] TRC #20: Wrote 3 bytes of 3 buffered data| net/Socket.hpp:1447
wsd-00001-00035 2023-03-07 08:37:46.465961 +0100 [ prisoner_poll ] TRC #19: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:46.465968 +0100 [ prisoner_poll ] TRC #20: setupPollFds getPollEvents: 0x1| net/Socket.hpp:862
wsd-00001-00035 2023-03-07 08:37:46.465976 +0100 [ prisoner_poll ] TRC ppoll start, timeoutMicroS: 5000000 size 2| net/Socket.cpp:338
wsd-00001-00035 2023-03-07 08:37:46.466039 +0100 [ prisoner_poll ] TRC Poll completed with 1 live polls max (5000000us)| net/Socket.cpp:357
wsd-00001-00035 2023-03-07 08:37:46.466095 +0100 [ prisoner_poll ] TRC #19: Starting handling poll results of prisoner_poll at index 0 (of 2): 0| net/Socket.cpp:436
wsd-00001-00035 2023-03-07 08:37:46.466109 +0100 [ prisoner_poll ] TRC #20: Revents: 0x1| net/Socket.hpp:1301
wsd-00001-00035 2023-03-07 08:37:46.466121 +0100 [ prisoner_poll ] TRC #20: Read 3 bytes in addition to 0 buffered bytes| net/Socket.hpp:1150
wsd-00001-00035 2023-03-07 08:37:46.466134 +0100 [ prisoner_poll ] TRC #20: Incoming data buffer 3 bytes, read result: 3, events: 0x1 (not closed)| net/Socket.hpp:1323
wsd-00001-00035 2023-03-07 08:37:46.466144 +0100 [ prisoner_poll ] TRC #20: Incoming WebSocket data of 3 bytes: 8A 01 00 | ...| net/WebSocketHandler.hpp:335
wsd-00001-00035 2023-03-07 08:37:46.466157 +0100 [ prisoner_poll ] TRC #20: Incoming WebSocket frame code 10, fin? true, mask? false, payload length: 1, residual socket data: 0 bytes.| net/WebSocketHandler.hpp:349
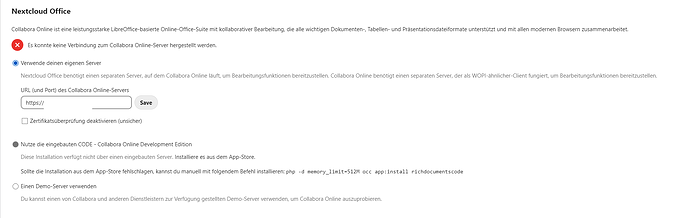
I can’t change the settings for WOPI IPs:
When using the Synology build in reverse proxy
I get this when running curl -vvv https://$NC_DOMAIN:443/hosting/discovery
bash-5.1# curl -vvv https://$NC_DOMAIN:443/hosting/discovery
exit
* Trying XX.XXX.XX.XX:443...
* Connected to sub.domain.com (XX.XXX.XX.XX) port 443 (#0)
* ALPN: offers h2
* ALPN: offers http/1.1
* CAfile: /etc/ssl/certs/ca-certificates.crt
* CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN: server accepted h2
* Server certificate:
* subject: CN=domain.com
* start date: Jan 5 12:43:16 2023 GMT
* expire date: Apr 5 12:43:15 2023 GMT
* subjectAltName: host "sub.domain.com" matched cert's "*.domain.com"
* issuer: C=US; O=Let's Encrypt; CN=R3
* SSL certificate verify ok.
* Using HTTP2, server supports multiplexing
* Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0
* h2h3 [:method: GET]
* h2h3 [:path: /hosting/discovery]
* h2h3 [:scheme: https]
* h2h3 [:authority: sub.domain.com]
* h2h3 [user-agent: curl/7.83.1]
* h2h3 [accept: */*]
* Using Stream ID: 1 (easy handle 0x7fc8da73a1b0)
> GET /hosting/discovery HTTP/2
> Host: sub.domain.com
> user-agent: curl/7.83.1
> accept: */*
>
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* old SSL session ID is stale, removing
* Connection state changed (MAX_CONCURRENT_STREAMS == 128)!
< HTTP/2 504
< date: Tue, 07 Mar 2023 07:49:29 GMT
< content-type: text/html
< content-length: 11939
< etag: "62a83cc4-2ea3"
<
<!DOCTYPE html>
<html>
<head>
<meta charset="utf-8">
<style>body{font-family:Arial,Helvetica,sans-serif;font-size:12px;text-align:center}h1{color:#06C;font-size:25px;line-height:60px;margin-top:56px}img{margin-top:40px}
</style>
</head>
<body>
<img src="data:image/jpg;base64,/9j/4AAQSkZJRgABAQEASABIAAD/2wBDAAEBAQEBAQEBAQEBAQEBAQEBAQEBAQEBAQEBAQECAQEB
AQEBAgICAgICAgICAgICAgICAgICAgICAgICAgICAgL/2wBDAQEBAQEBAQICAgICAgICAgICAgIC
AgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgICAgL/wAARCAAzAMgDAREA
AhEBAxEB/8QAHwAAAgIDAAMBAQAAAAAAAAAAAAkICgEGBwQFCwMC/8QARBAAAAYCAAUCBQIDAwYP
...
...
...
"/>
<h1 id="a"></h1>
<hr>
<p>© 2022 <a href="http://www.synology.com">Synology Inc.</a></p>
</body>
<script type ="text/javascript">
/* Copyright (c) 2022 Synology Inc. All rights reserved. */
(function(){var a={en:"Sorry, the page you are looking for is not found.",zh:"\u62b1\u6b49\uff0c\u60a8\u6240\u6307\u5b9a\u7684\u9875\u9762\u4e0d\u5b58\u5728\u3002",it:"La pagina richiesta non \u00e8 stata trovata.","zh-HK":"\u62b1\u6b49\uff0c\u60a8\u6240\u6307\u5b9a\u7684\u9801\u9762\u4e0d\u5b58\u5728\u3002",cs:"Hledan\u00e1 str\u00e1nka nebyla nalezena.",es:"Lo sentimos, no se encuentra la p\u00e1gina que est\u00e1 buscando.",ru:"\u0418\u0437\u0432\u0438\u043d\u0438\u0442\u0435, \u0438\u0441\u043a\u043e\u043c\u0430\u044f \u0432\u0430\u043c\u0438 \u0441\u0442\u0440\u0430\u043d\u0438\u0446\u0430 \u043d\u0435 \u043d\u0430\u0439\u0434\u0435\u043d\u0430.",nl:"Sorry, de pagina die u zoekt kan niet weergegeven worden.",pt:"Desculpe, a p\u00e1gina que procura n\u00e3o foi encontrada.",no:"Beklager, siden du leter etter finnes ikke.",nb:"Beklager, siden du leter etter finnes ikke.",tr:"\u00dczg\u00fcn\u00fcz, arad\u0131\u011f\u0131n\u0131z sayfa bulunamad\u0131.",pl:"Przepraszamy, nie znaleziono strony, kt\u00f3rej szukasz.",fr:"D\u00e9sol\u00e9, la page que vous recherchez est introuvable.",de:"Es tut uns Leid, die von Ihnen gesuchte Seite konnte nicht gefunden werden.",da:"Desv\u00e6rre, den side, du leder efter, kunne ikke findes.","pt-BR":"Desculpe, a p\u00e1gina que procura n\u00e3o foi encontrada.","zh-MO":"\u62b1\u6b49\uff0c\u60a8\u6240\u6307\u5b9a\u7684\u9801\u9762\u4e0d\u5b58\u5728\u3002",hu:"Eln\u00e9z\u00e9st, a keresett oldal nem tal\u00e1lhat\u00f3.",ja:"\u7533\u3057\u8a33\u3042\u308a\u307e\u305b\u3093\u304c\u3001\u635c\u3057\u3066\u3044\u308b\u30da\u30fc\u30b8\u304c\u898b\u3064\u304b\u308a\u307e\u305b\u3093",nn:"Beklager, siden du leter etter finnes ikke.","zh-TW":"\u62b1\u6b49\uff0c\u60a8\u6240\u6307\u5b9a\u7684\u9801\u9762\u4e0d\u5b58\u5728\u3002",ko:"\uc8c4\uc1a1\ud569\ub2c8\ub2e4. \ucc3e\uace0\uc790 \ud558\ub294 \ud398\uc774\uc9c0\ub97c \ubc1c\uacac\ud558\uc9c0 \ubabb\ud588\uc2b5\ub2c8\ub2e4.",sv:"Sidan du s\u00f6ker hittades inte."};var b=window.navigator.browserLanguage||window.navigator.language;if(-1==["zh-TW","zh-MO","zh-HK","pt-BR"].indexOf(b)){b=b.split("-",1)}document.getElementById("a").innerHTML=a[b]||a.en})();
</script>
</html>
* Connection #0 to host sub.domain.com left intact
exit
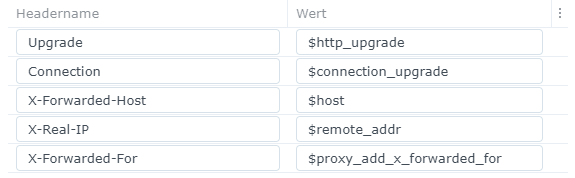
I added a .conf to /etc/nginx/conf.d/ with the following :
map $http_upgrade $connection_upgrade {
default upgrade;
'' close;
}
server {
listen 80;
listen [::]:80; # comment to disable IPv6
if ($scheme = "http") {
return 301 https://$host$request_uri;
}
listen 443 ssl http2;
listen [::]:443 ssl http2; # comment to disable IPv6
server_name sub.domain.com;
location / {
resolver localhost; # Note: you need to set a valid dns resolver here or use 127.0.0.1 / [::1] instead of localhost in the line below. See https://stackoverflow.com/a/49642310 for a better explanation
proxy_pass http://localhost:11000$request_uri; # Note: you need to change localhost to 127.0.0.1 or [::1], if you don't use a valid dns resolver in the line above
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header Early-Data $ssl_early_data;
proxy_set_header X-Forwarded-Scheme $scheme;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header Accept-Encoding "";
proxy_set_header Host $host;
client_body_buffer_size 512k;
proxy_read_timeout 86400s;
client_max_body_size 0;
# Websocket
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $connection_upgrade;
}
ssl_certificate /usr/syno/etc/certificate/_archive/eH24dC/fullchain.pem; # managed by certbot on host machine
ssl_certificate_key /usr/syno/etc/certificate/_archive/eH24dC/privkey.pem; # managed by certbot on host machine
ssl_early_data on;
ssl_session_timeout 1d;
ssl_session_cache shared:MozSSL:10m; # about 40000 sessions
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384;
ssl_prefer_server_ciphers off;
}
Now there is no error page with the lookup:
bash-5.1# curl -vvv https://$NC_DOMAIN:443/hosting/discovery
* Trying XX.XXX.XX.XX:443...
* Connected to sub.domain.com (XX.XXX.XX.XX) port 443 (#0)
* ALPN: offers h2
* ALPN: offers http/1.1
* CAfile: /etc/ssl/certs/ca-certificates.crt
* CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS handshake, Encrypted Extensions (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN: server accepted h2
* Server certificate:
* subject: CN=domain.com
* start date: Jan 5 12:43:16 2023 GMT
* expire date: Apr 5 12:43:15 2023 GMT
* subjectAltName: host "sub.domain.com" matched cert's "*.domain.com"
* issuer: C=US; O=Let's Encrypt; CN=R3
* SSL certificate verify ok.
* Using HTTP2, server supports multiplexing
* Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0
* h2h3 [:method: GET]
* h2h3 [:path: /hosting/discovery]
* h2h3 [:scheme: https]
* h2h3 [:authority: sub.domain.com]
* h2h3 [user-agent: curl/7.83.1]
* h2h3 [accept: */*]
* Using Stream ID: 1 (easy handle 0x7f2fce75d1b0)
> GET /hosting/discovery HTTP/2
> Host: sub.domain.com
> user-agent: curl/7.83.1
> accept: */*
>
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* old SSL session ID is stale, removing
* Connection state changed (MAX_CONCURRENT_STREAMS == 128)!
< HTTP/2 502
< date: Tue, 07 Mar 2023 08:01:23 GMT
< content-length: 0
<
* Connection #0 to host sub.domain.com left intact
bash-5.1#
Does anybody have an idea what might be wrong?