Hi all,
So I’ve been using Nextcloud + redis + mariadb + fpm-alpine + let’s encrypt + cron based on the docker-compose.yml file and content from https://github.com/nextcloud/docker/tree/master/.examples/docker-compose/with-nginx-proxy/mariadb-cron-redis/fpm with great success since a few Nextcloud releases, and I’m now on Nextcloud 17.
So all is working well deployed in a VM with public internet access, proper FQDN and Let’s Encrypt certificate.
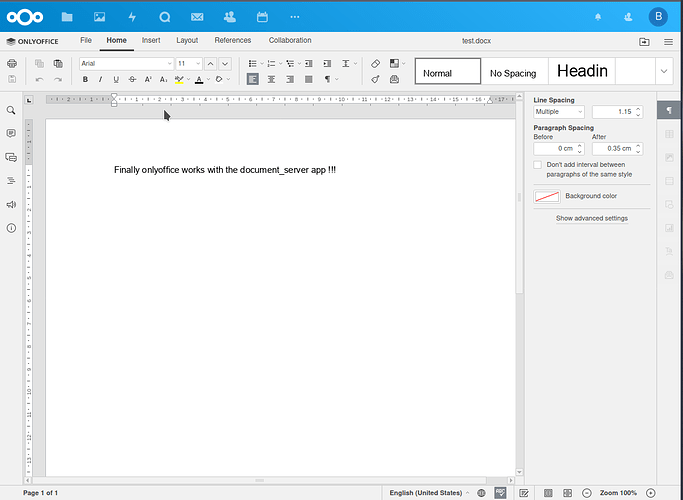
I’ve recently started to look at integrating onlyoffice with this, so I incorporated some bits from https://github.com/ONLYOFFICE/docker-onlyoffice-nextcloud in my configuration.
I’m able to see the onlyoffice document server public welcome page  :
:
The onlyoffice setting in the companion app seem to be accepted/validated, I’ve tried either with the public domain name or with the internal container names, but whenever I try to open an office file I’ve got the quite “usual” error message:
ONLYOFFICE cannot be reached. Please contact admin
I can’t find anything meaningful in the logs 
Here is the docker-compose.yml:
version: '3'
services:
# MySQL database for Nextcloud
db:
image: mariadb
command: --transaction-isolation=READ-COMMITTED --binlog-format=ROW
restart: always
volumes:
- db:/var/lib/mysql
environment:
- MYSQL_ROOT_PASSWORD=XXXXXXXXXXXX
env_file:
- db.env
# Redis server for memory caching for Nextcloud
redis:
image: redis:alpine
restart: always
# Nextcloud application
app:
image: nextcloud:17-fpm-alpine
restart: always
volumes:
- nextcloud:/var/www/html
environment:
- MYSQL_HOST=db
- REDIS_HOST=redis
env_file:
- db.env
depends_on:
- db
- redis
# nginx container, exposing nextcloud app
web:
build: ./web
restart: always
volumes:
- nextcloud:/var/www/html:ro
environment:
- VIRTUAL_HOST=mydomain.tld
- LETSENCRYPT_HOST=mydomain.tld
- LETSENCRYPT_EMAIL=me@mydomain.tld
depends_on:
- app
networks:
- proxy-tier
- default
# cron container based on Nextcloud image
cron:
image: nextcloud:17-fpm-alpine
restart: always
volumes:
- nextcloud:/var/www/html
entrypoint: /cron.sh
depends_on:
- db
- redis
# Web facing nginx proxy, integrating with Let's Encrypt
proxy:
build: ./proxy
restart: always
ports:
- 80:80
- 443:443
labels:
com.github.jrcs.letsencrypt_nginx_proxy_companion.nginx_proxy: "true"
volumes:
- certs:/etc/nginx/certs:ro
- vhost.d:/etc/nginx/vhost.d
- html:/usr/share/nginx/html
- /var/run/docker.sock:/tmp/docker.sock:ro
networks:
- proxy-tier
# Let's Encrypt companion app to handle certificate
letsencrypt-companion:
image: jrcs/letsencrypt-nginx-proxy-companion
restart: always
volumes:
- certs:/etc/nginx/certs
- vhost.d:/etc/nginx/vhost.d
- html:/usr/share/nginx/html
- /var/run/docker.sock:/var/run/docker.sock:ro
networks:
- proxy-tier
depends_on:
- proxy
# Onlyoffice document server
#
# https://github.com/ONLYOFFICE/docker-onlyoffice-nextcloud/blob/master/docker-compose.yml
onlyoffice-document-server:
image: onlyoffice/documentserver:latest
stdin_open: true
tty: true
restart: always
depends_on:
- app
expose:
- '80'
- '443'
volumes:
- document_data:/var/www/onlyoffice/Data
- document_log:/var/log/onlyoffice
volumes:
db:
nextcloud:
certs:
vhost.d:
html::champagne:
document_data:
document_log:
networks:
proxy-tier:
And the nginx.conf for the web container:
worker_processes auto;
error_log /var/log/nginx/error.log warn;
pid /var/run/nginx.pid;
events {
worker_connections 1024;
}
http {
include /etc/nginx/mime.types;
default_type application/octet-stream;
log_format main '$remote_addr - $remote_user [$time_local] "$request" '
'$status $body_bytes_sent "$http_referer" '
'"$http_user_agent" "$http_x_forwarded_for"';
access_log /var/log/nginx/access.log main;
sendfile on;
#tcp_nopush on;
keepalive_timeout 65;
set_real_ip_from 10.0.0.0/8;
set_real_ip_from 172.16.0.0/12;
set_real_ip_from 192.168.0.0/16;
real_ip_header X-Real-IP;
#gzip on;
upstream php-handler {
server app:9000;
}
server {
listen 80;
# Add headers to serve security related headers
# Before enabling Strict-Transport-Security headers please read into this
# topic first.
#add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;" always;
#
# WARNING: Only add the preload option once you read about
# the consequences in https://hstspreload.org/. This option
# will add the domain to a hardcoded list that is shipped
# in all major browsers and getting removed from this list
# could take several months.
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Download-Options "noopen" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "none" always;
add_header X-XSS-Protection "1; mode=block" always;
# Remove X-Powered-By, which is an information leak
fastcgi_hide_header X-Powered-By;
# Path to the root of your installation
root /var/www/html;
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
# The following 2 rules are only needed for the user_webfinger app.
# Uncomment it if you're planning to use this app.
#rewrite ^/.well-known/host-meta /public.php?service=host-meta last;
#rewrite ^/.well-known/host-meta.json /public.php?service=host-meta-json last;
# The following rule is only needed for the Social app.
# Uncomment it if you're planning to use this app.
#rewrite ^/.well-known/webfinger /public.php?service=webfinger last;
location = /.well-known/carddav {
return 301 $scheme://$host/remote.php/dav;
}
location = /.well-known/caldav {
return 301 $scheme://$host/remote.php/dav;
}
# set max upload size
client_max_body_size 10G;
fastcgi_buffers 64 4K;
# Enable gzip but do not remove ETag headers
gzip on;
gzip_vary on;
gzip_comp_level 4;
gzip_min_length 256;
gzip_proxied expired no-cache no-store private no_last_modified no_etag auth;
gzip_types application/atom+xml application/javascript application/json application/ld+json application/manifest+json application/rss+xml application/vnd.geo+json application/vnd.ms-fontobject application/x-font-ttf application/x-web-app-manifest+json application/xhtml+xml application/xml font/opentype image/bmp image/svg+xml image/x-icon text/cache-manifest text/css text/plain text/vcard text/vnd.rim.location.xloc text/vtt text/x-component text/x-cross-domain-policy;
# Uncomment if your server is build with the ngx_pagespeed module
# This module is currently not supported.
#pagespeed off;
location / {
rewrite ^ /index.php;
}
location ~ ^\/(?:build|tests|config|lib|3rdparty|templates|data)\/ {
deny all;
}
location ~ ^\/(?:\.|autotest|occ|issue|indie|db_|console) {
deny all;
}
location ~ ^\/(?:index|remote|public|cron|core\/ajax\/update|status|ocs\/v[12]|updater\/.+|oc[ms]-provider\/.+)\.php(?:$|\/) {
fastcgi_split_path_info ^(.+?\.php)(\/.*|)$;
set $path_info $fastcgi_path_info;
try_files $fastcgi_script_name =404;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $path_info;
# fastcgi_param HTTPS on;
# Avoid sending the security headers twice
fastcgi_param modHeadersAvailable true;
# Enable pretty urls
fastcgi_param front_controller_active true;
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
}
location ~ ^\/(?:updater|oc[ms]-provider)(?:$|\/) {
try_files $uri/ =404;
index index.php;
}
# Adding the cache control header for js, css and map files
# Make sure it is BELOW the PHP block
location ~ \.(?:css|js|woff2?|svg|gif|map)$ {
try_files $uri /index.php$request_uri;
add_header Cache-Control "public, max-age=15778463";
# Add headers to serve security related headers (It is intended to
# have those duplicated to the ones above)
# Before enabling Strict-Transport-Security headers please read into
# this topic first.
#add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;" always;
#
# WARNING: Only add the preload option once you read about
# the consequences in https://hstspreload.org/. This option
# will add the domain to a hardcoded list that is shipped
# in all major browsers and getting removed from this list
# could take several months.
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Download-Options "noopen" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "none" always;
add_header X-XSS-Protection "1; mode=block" always;
# Optional: Don't log access to assets
access_log off;
}
location ~ \.(?:png|html|ttf|ico|jpg|jpeg|bcmap)$ {
try_files $uri /index.php$request_uri;
# Optional: Don't log access to other assets
access_log off;
}
# https://github.com/ONLYOFFICE/docker-onlyoffice-nextcloud/blob/master/nginx.conf
location ~* ^/ds-vpath/ {
rewrite /ds-vpath/(.*) /$1 break;
proxy_pass http://onlyoffice-document-server;
proxy_redirect off;
client_max_body_size 100m;
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
I was a bit surprise to not find any existing example using the offici
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Host $host/ds-vpath;
proxy_set_header X-Forwarded-Proto $http_x_forwarded_proto;
}
}
}
My companion app configuration is currently:
- Document Editing Service address: https ://mydomain.tld/ds-vpath/
- Document Editing Service address for internal requests from the server: http ://onlyoffice-document-server/
- Server address for internal requests from the Document Editing Service: http ://web/
Without more success I’ve also tried with:
- Document Editing Service address: https ://mydomain.tld/ds-vpath/
- Document Editing Service address for internal requests from the server: https ://mydomain.tld/ds-vpath/
- Server address for internal requests from the Document Editing Service: https ://mydomain.tld/
(the links are correct, it’s just that I’m not allowed to add more than 4 links)
So this a bit beyond my actual understanding/knowledge and I probably made a mistake somewhere, but I’m not sure where.
I’ve looked at various tickets/messages/examples here and ther but wasn’t able to find something that sound appropriate.
So I’m not able to figure what I should do to get this working, so if anyone has an idea on how to do this…
Thanks for any help!