Hallo,
ich versuche eine saubere Installation der NextCloud unter nginx hinzubekommen. Mit apache2 und NextCloud habe ich über die Jahre einiges an Erfahrungen und Wissen aufgebaut. Aber ich will meine NextCloud-Installationen auf nginx umziehen und suche nach der funktionierenden Musterlösung mit ISPConfig (d.h., ich brauche nur die ausreichenden Direktiven und nicht die komplette Webserver-Konfiguration).
Zwar funktioniert mit der Konfiguration (s.u.) das Nötige (Dateien hochladen auch mit drag’n&drop, Dateien teilen/kopieren/verschieben/löschen, Dateien herunterladen).
Aber Zugriff via App (Android) wird verweigert.
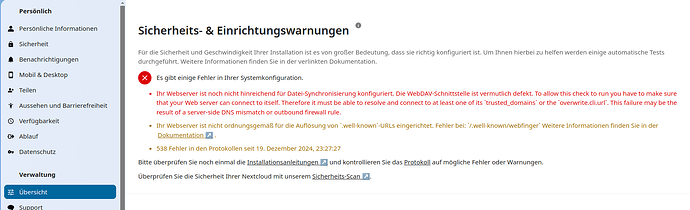
Die beiden Fehlermeldungen verunsichern mich. Ich scheitere im Moment an diesen zwei Fehlermeldungen:
Laut NGINX configuration — Nextcloud latest Administration Manual latest documentation gibt es den Eintrag für .well-known webfinger nicht, trotzdem wird er hier genannt.
Die Meldung bzgl. trusted_domains und overwrite.cli.url bringt mich auch nicht weiter, da in der config/config.php (mit verschiedenen Varianten ausprobiert) berücksichtigt. Die Andeutung, dass DNS oder Firewall ein Problem sein könnten, kann ich mit großer Sicherheit ausschließen.
Ist es ein Bug und mit der nächsten Version ist diese Meldung weg?
Kann NextCloud nicht mit nginx betrieben werden?
Konfiguration:
- Neuer Server eingerichtet, mit Debian 12.8, PHP8.3, nginx 1.22.1, MariaDB/MySQL, Redis-Server etc. UND ISPConfig
- NextCloud-Installation Version 30.0.4.1
- PHP-Einstellungen:
memory_limit = 512M
max_execution_time = 300
max_input_time = -1
always_populate_raw_post_data=-1
extension=apcu.so
apc.enable_cli=1
opcache.jit = 1255
opcache.jit_buffer_size = 128M
opcache.enable=1
opcache.enable_cli=1
opcache.interned_strings_buffer=128
opcache.max_accelerated_files=10000
opcache.memory_consumption=512
opcache.save_comments=1
opcache.revalidate_freq=60
opcache.validate_timestamps = 0
- nginx-Direktiven
##subroot /nextcloud ##
# Set the `immutable` cache control options only for assets with a cache busting `v` argument
map $arg_v $asset_immutable {
"" "";
default ", immutable";
}
# set max upload size and increase upload timeout:
client_max_body_size 800M;
client_body_timeout 1800s;
fastcgi_buffers 64 4K;
# Enable gzip but do not remove ETag headers
gzip on;
gzip_vary on;
gzip_comp_level 4;
gzip_min_length 256;
gzip_proxied expired no-cache no-store private no_last_modified no_etag auth;
gzip_types application/atom+xml text/javascript application/javascript application/json application/ld+json application/manifest+json application/rss+xml application/vnd.geo+json application/vnd.ms-fontobject application/wasm application/x-font-ttf application/x-web-app-manifest+json application/xhtml+xml application/xml font/opentype image/bmp image/svg+xml image/x-icon text/cache-manifest text/css text/plain text/vcard text/vnd.rim.location.xloc text/vtt text/x-component text/x-cross-domain-policy;
# The settings allows you to optimize the HTTP2 bandwidth.
# See https://blog.cloudflare.com/delivering-http-2-upload-speed-improvements/
# for tuning hints
client_body_buffer_size 512k;
# HTTP response headers borrowed from Nextcloud .htaccess
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "noindex, nofollow" always;
add_header X-XSS-Protection "1; mode=block" always;
# Remove X-Powered-By, which is an information leak
fastcgi_hide_header X-Powered-By;
# Set .mjs and .wasm MIME types
include mime.types;
types {
text/javascript js mjs;
application/wasm wasm;
}
# Rule borrowed from `.htaccess` to handle Microsoft DAV clients
location = / {
if ( $http_user_agent ~ ^DavClnt ) {
return 302 /remote.php/webdav/$is_args$args;
}
}
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
# Make a regex exception for `/.well-known` so that clients can still
# access it despite the existence of the regex rule
# `location ~ /(\.|autotest|...)` which would otherwise handle requests
# for `/.well-known`.
location ^~ /.well-known {
# The rules in this block are an adaptation of the rules
# in `.htaccess` that concern `/.well-known`.
location = /.well-known/carddav { return 301 /remote.php/dav/; }
location = /.well-known/caldav { return 301 /remote.php/dav/; }
location /.well-known/acme-challenge { try_files $uri $uri/ =404; }
location /.well-known/pki-validation { try_files $uri $uri/ =404; }
# Let Nextcloud's API for `/.well-known` URIs handle all other
# requests by passing them to the front-end controller.
return 301 /index.php$request_uri;
}
# Rules borrowed from `.htaccess` to hide certain paths from clients
location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)(?:$|/) { return 404; }
location ~ ^/(?:\.|autotest|occ|issue|indie|db_|console) { return 404; }
# Ensure this block, which passes PHP files to the PHP process, is above the blocks
# which handle static assets (as seen below). If this block is not declared first,
# then Nginx will encounter an infinite rewriting loop when it prepends `/index.php`
# to the URI, resulting in a HTTP 500 error response.
location ~ \.php(?:$|/) {
# Required for legacy support
rewrite ^/(?!index|remote|public|cron|core\/ajax\/update|status|ocs\/v[12]|updater\/.+|ocs-provider\/.+|.+\/richdocumentscode(_arm64)?\/proxy) /index.php$request_uri;
fastcgi_split_path_info ^(.+?\.php)(/.*)$;
set $path_info $fastcgi_path_info;
try_files $fastcgi_script_name =404;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $path_info;
fastcgi_param HTTPS on;
fastcgi_param modHeadersAvailable true; # Avoid sending the security headers twice
fastcgi_param front_controller_active true; # Enable pretty urls
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
fastcgi_max_temp_file_size 0;
}
# Serve static files
location ~ \.(?:css|js|mjs|svg|gif|ico|jpg|png|webp|wasm|tflite|map|ogg|flac)$ {
try_files $uri /index.php$request_uri;
# HTTP response headers borrowed from Nextcloud `.htaccess`
add_header Cache-Control "public, max-age=15778463$asset_immutable";
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "noindex, nofollow" always;
add_header X-XSS-Protection "1; mode=block" always;
access_log off; # Optional: Don't log access to assets
}
location ~ \.(otf|woff2?)$ {
try_files $uri /index.php$request_uri;
expires 7d; # Cache-Control policy borrowed from `.htaccess`
access_log off; # Optional: Don't log access to assets
}
# Rule borrowed from `.htaccess`
location /remote {
return 301 /remote.php$request_uri;
}
location / {
try_files $uri $uri/ /index.php$request_uri;
}
- config/config.php
<?php
$CONFIG = array (
'instanceid' => 'xxxxxxxxxxxx',
'passwordsalt' => 'xxxxxxxxxxxx',
'secret' => 'xxxxxxxxxxxx',
'trusted_domains' =>
array (
0 => 'nc-test.example.com',
1 => 'my-server.com',
2 => 'xxx.xxx.xxx.xxx',
),
'datadirectory' => '/var/www/clients/clientx/weby/web/nextcloud/data',
'dbtype' => 'mysql',
'version' => '30.0.4.1',
'overwrite.cli.url' => 'https://nc-test.example.com/nextcloud',
'dbname' => 'xxxxxxxxxxxx',
'dbhost' => 'localhost',
'dbport' => '',
'dbtableprefix' => 'oc_',
'mysql.utf8mb4' => true,
'dbuser' => 'xxxxxxxxxxxx',
'dbpassword' => 'xxxxxxxxxxxx',
'installed' => true,
'mail_from_address' => 'xxxxxxxxxxxx',
'mail_smtpmode' => 'smtp',
'mail_sendmailmode' => 'smtp',
'mail_domain' => 'xxxxxxxxxxxx',
'mail_smtphost' => 'xxxxxxxxxxxx',
'mail_smtpport' => '25',
'mail_smtpauth' => 1,
'mail_smtpname' => 'xxxxxxxxxxxx',
'mail_smtppassword' => 'xxxxxxxxxxxx',
'default_phone_region' => 'DE',
'has_rebuilt_cache' => true,
'memcache.local' => '\\OC\\Memcache\\APCu',
'filelocking.enabled' => true,
'memcache.locking' => '\\OC\\Memcache\\Redis',
'redis' =>
array (
'host' => 'localhost',
'port' => 6379,
'timeout' => 0.0,
'password' => '',
),
'maintenance_window_start' => '1',
'maintenance' => false,
'loglevel' => 2,
'loglevel_frontend' => 2,
'check_for_working_wellknown_setup' => true,
);