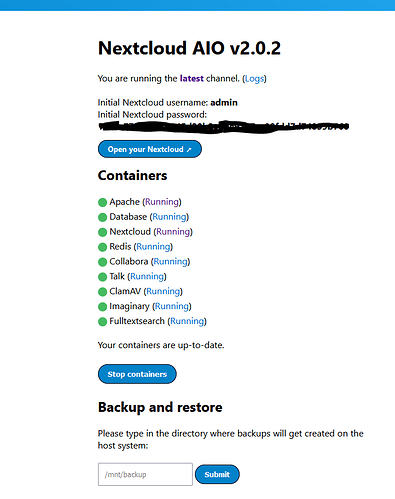
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
383f1a41007c nextcloud/aio-apache:latest "start.sh /usr/bin/s…" 2 hours ago Exited (0) 2 hours ago nextcloud-aio-apache
3ba6b8c4f1a3 nextcloud/aio-nextcloud:latest "/start.sh /usr/bin/…" 2 hours ago Up 3 minutes (healthy) 9000/tcp nextcloud-aio-nextcloud
cd4c52ccbed4 nextcloud/aio-redis:latest "start.sh" 2 hours ago Up 3 minutes (healthy) 6379/tcp nextcloud-aio-redis
76373d6284c6 nextcloud/aio-postgresql:latest "start.sh" 2 hours ago Up 3 minutes (healthy) 5432/tcp nextcloud-aio-database
e095b4519a3f nextcloud/aio-domaincheck:latest "/start.sh" 2 hours ago Exited (137) 2 hours ago nextcloud-aio-domaincheck
2fd1ccd07a19 nextcloud/all-in-one:latest "start.sh /usr/bin/s…" 2 hours ago Up 3 minutes (healthy) 0.0.0.0:80->80/tcp, :::80->80/tcp, 0.0.0.0:8080->8080/tcp, :::8080->8080/tcp, 0.0.0.0:8443->8443/tcp, :::8443->8443/tcp nextcloud-aio-mastercontainer
Apache Log:
Waiting for Nextcloud to start...
nc: getaddrinfo for host "nextcloud-aio-nextcloud" port 9000: Name or service not known
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
Waiting for Nextcloud to start...
AH00558: apache2: Could not reliably determine the server's fully qualified domain name, using 172.17.0.6. Set the 'ServerName' directive globally to suppress this message
{"level":"info","ts":1663834651.4324899,"msg":"using provided configuration","config_file":"/Caddyfile","config_adapter":""}
{"level":"warn","ts":1663834651.4346657,"msg":"Caddyfile input is not formatted; run the 'caddy fmt' command to fix inconsistencies","adapter":"caddyfile","file":"/Caddyfile","line":2}
{"level":"info","ts":1663834651.4358983,"logger":"admin","msg":"admin endpoint started","address":"tcp/localhost:2019","enforce_origin":false,"origins":["//localhost:2019","//[::1]:2019","//127.0.0.1:2019"]}
{"level":"info","ts":1663834651.4362164,"logger":"tls.cache.maintenance","msg":"started background certificate maintenance","cache":"0xc0003924d0"}
{"level":"info","ts":1663834651.4362478,"logger":"http","msg":"server is listening only on the HTTPS port but has no TLS connection policies; adding one to enable TLS","server_name":"srv0","https_port":443}
{"level":"warn","ts":1663834651.4362597,"logger":"http","msg":"automatic HTTP->HTTPS redirects are disabled","server_name":"srv0"}
{"level":"info","ts":1663834651.437259,"logger":"tls","msg":"cleaning storage unit","description":"FileStorage:/mnt/data/caddy"}
{"level":"info","ts":1663834651.4373107,"logger":"tls","msg":"finished cleaning storage units"}
{"level":"info","ts":1663834651.4374712,"logger":"http","msg":"enabling automatic TLS certificate management","domains":["c.meyer.de"]}
{"level":"info","ts":1663834651.4379838,"msg":"autosaved config (load with --resume flag)","file":"/var/www/.config/caddy/autosave.json"}
{"level":"info","ts":1663834651.4380043,"msg":"serving initial configuration"}
{"level":"info","ts":1663834651.4384208,"logger":"tls.obtain","msg":"acquiring lock","identifier":"c.meyer.de"}
{"level":"info","ts":1663834651.4411757,"logger":"tls.obtain","msg":"lock acquired","identifier":"c.meyer.de"}
{"level":"info","ts":1663834652.2783682,"logger":"tls.issuance.acme","msg":"waiting on internal rate limiter","identifiers":["c.meyer.de"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1663834652.2784834,"logger":"tls.issuance.acme","msg":"done waiting on internal rate limiter","identifiers":["c.meyer.de"],"ca":"https://acme-v02.api.letsencrypt.org/directory","account":""}
{"level":"info","ts":1663834652.7654939,"logger":"tls.issuance.acme.acme_client","msg":"trying to solve challenge","identifier":"c.meyer.de","challenge_type":"tls-alpn-01","ca":"https://acme-v02.api.letsencrypt.org/directory"}
{"level":"error","ts":1663834654.1353533,"logger":"tls.issuance.acme.acme_client","msg":"challenge failed","identifier":"c.meyer.de","challenge_type":"tls-alpn-01","problem":{"type":"urn:ietf:params:acme:error:unauthorized","title":"","detail":"Cannot negotiate ALPN protocol \"acme-tls/1\" for tls-alpn-01 challenge","instance":"","subproblems":[]}}
{"level":"error","ts":1663834654.1354105,"logger":"tls.issuance.acme.acme_client","msg":"validating authorization","identifier":"c.meyer.de","problem":{"type":"urn:ietf:params:acme:error:unauthorized","title":"","detail":"Cannot negotiate ALPN protocol \"acme-tls/1\" for tls-alpn-01 challenge","instance":"","subproblems":[]},"order":"https://acme-v02.api.letsencrypt.org/acme/order/743275557/127787781647","attempt":1,"max_attempts":3}
{"level":"error","ts":1663834654.1354535,"logger":"tls.obtain","msg":"could not get certificate from issuer","identifier":"c.meyer.de","issuer":"acme-v02.api.letsencrypt.org-directory","error":"HTTP 403 urn:ietf:params:acme:error:unauthorized - Cannot negotiate ALPN protocol \"acme-tls/1\" for tls-alpn-01 challenge"}
{"level":"error","ts":1663834654.1354778,"logger":"tls.obtain","msg":"will retry","error":"[c.meyer.de] Obtain: [c.meyer.de] solving challenge: c.meyer.de: [c.meyer.de] authorization failed: HTTP 403 urn:ietf:params:acme:error:unauthorized - Cannot negotiate ALPN protocol \"acme-tls/1\" for tls-alpn-01 challenge (ca=https://acme-v02.api.letsencrypt.org/directory)","attempt":1,"retrying_in":60,"elapsed":2.694256894,"max_duration":2592000}
{"level":"info","ts":1663834703.1944914,"msg":"shutting down apps, then terminating","signal":"SIGTERM"}
{"level":"warn","ts":1663834703.194546,"msg":"exiting; byeee!! 👋","signal":"SIGTERM"}
{"level":"info","ts":1663834703.195875,"logger":"tls.cache.maintenance","msg":"stopped background certificate maintenance","cache":"0xc0003924d0"}
{"level":"info","ts":1663834703.1959393,"logger":"tls.obtain","msg":"releasing lock","identifier":"c.meyer.de"}
{"level":"error","ts":1663834703.1961439,"logger":"tls.obtain","msg":"unable to unlock","identifier":"c.meyer.de","lock_key":"issue_cert_c.meyer.de","error":"remove /mnt/data/caddy/locks/issue_cert_c.meyer.de.lock: no such file or directory"}
{"level":"error","ts":1663834703.1961849,"logger":"tls","msg":"job failed","error":"c.meyer.de: obtaining certificate: context canceled"}
{"level":"info","ts":1663834703.197529,"logger":"admin","msg":"stopped previous server","address":"tcp/localhost:2019"}
{"level":"info","ts":1663834703.197552,"msg":"shutdown complete","signal":"SIGTERM","exit_code":0}
Firewal Log:
192.168.144.90 = Nextcloud
192.168.144.253 = Opnsense with HA Proxy
192.168.144.52.2814 > 192.168.252.253.9292: Flags [S], cksum 0x0e38 (correct), seq 1143265525, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.214011 rule 67/0(match): pass in on em1: (tos 0x0, ttl 127, id 41599, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2815 > 192.168.252.253.9292: Flags [S], cksum 0xd969 (correct), seq 643705737, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.001514 rule 67/0(match): pass in on em1: (tos 0x0, ttl 127, id 41601, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2816 > 192.168.252.253.9292: Flags [S], cksum 0x9293 (correct), seq 1175409325, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.000745 rule 67/0(match): pass in on em1: (tos 0x0, ttl 127, id 41603, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2817 > 192.168.252.253.9292: Flags [S], cksum 0x6faf (correct), seq 1807765471, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.000835 rule 67/0(match): pass in on em1: (tos 0x0, ttl 127, id 41605, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2818 > 192.168.252.253.9292: Flags [S], cksum 0x50e4 (correct), seq 3097829828, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.005110 rule 67/0(match): pass in on em1: (tos 0x0, ttl 127, id 41616, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2819 > 192.168.252.253.9292: Flags [S], cksum 0xa4b9 (correct), seq 4151152421, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.220121 rule 66/0(match): pass in on em1: (tos 0x0, ttl 51, id 46203, offset 0, flags [DF], proto TCP (6), length 60)
80.187.65.179.9164 > 192.168.252.253.443: Flags [S], cksum 0x325b (correct), seq 982578561, win 65535, options [mss 1340,sackOK,TS val 93219552 ecr 0,nop,wscale 8], length 0
00:00:00.009273 rule 66/0(match): pass in on em1: (tos 0x0, ttl 51, id 41577, offset 0, flags [DF], proto TCP (6), length 60)
80.187.65.179.9165 > 192.168.252.253.443: Flags [S], cksum 0x995f (correct), seq 2511745874, win 65535, options [mss 1340,sackOK,TS val 93219556 ecr 0,nop,wscale 8], length 0
00:00:00.104391 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59513 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x4f32), seq 1265648558, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 3868189132 ecr 0], length 0
00:00:00.039332 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59514 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x073c), seq 3439798714, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 2762802177 ecr 0], length 0
00:00:01.735475 rule 66/0(match): pass in on em1: (tos 0x0, ttl 126, id 52528, offset 0, flags [DF], proto TCP (6), length 52)
192.168.254.83.60377 > 192.168.252.253.443: Flags [S], cksum 0x1747 (correct), seq 663210918, win 64240, options [mss 1319,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.238521 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59515 > 192.168.144.90.8080: Flags [S], cksum 0xb8d7 (incorrect -> 0x24a7), seq 233517909, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 3307560305 ecr 0], length 0
00:00:00.941569 rule 66/0(match): pass in on em1: (tos 0x0, ttl 127, id 41867, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2821 > 192.168.252.253.443: Flags [S], cksum 0x566e (correct), seq 2857192736, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.013327 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59516 > 192.168.144.90.11000: Flags [S], cksum 0xb8d7 (incorrect -> 0x5b8c), seq 2285815403, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 774414442 ecr 0], length 0
00:00:00.443139 rule 66/0(match): pass in on em1: (tos 0x0, ttl 127, id 41876, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2822 > 192.168.252.253.443: Flags [S], cksum 0xcc85 (correct), seq 1782912784, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.006810 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59517 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x5877), seq 849581123, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 1002261390 ecr 0], length 0
00:00:00.590722 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59518 > 192.168.144.90.11000: Flags [S], cksum 0xb8d7 (incorrect -> 0xdeeb), seq 1996881397, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 215817295 ecr 0], length 0
00:00:01.012133 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59519 > 192.168.144.90.11000: Flags [S], cksum 0xb8d7 (incorrect -> 0x6453), seq 2147586077, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 3092795463 ecr 0], length 0
00:00:00.402006 rule 66/0(match): pass in on em1: (tos 0x2,ECT(0), ttl 127, id 17022, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.11.51993 > 192.168.252.253.443: Flags [SEW], cksum 0x805e (correct), seq 880662612, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.007758 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59520 > 192.168.144.90.8080: Flags [S], cksum 0xb8d7 (incorrect -> 0x32a4), seq 2335711402, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 1941517881 ecr 0], length 0
00:00:00.635460 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59521 > 192.168.144.90.11000: Flags [S], cksum 0xb8d7 (incorrect -> 0x83f3), seq 2696033783, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 873393764 ecr 0], length 0
00:00:01.447019 rule 66/0(match): pass in on em1: (tos 0x0, ttl 127, id 41886, offset 0, flags [DF], proto TCP (6), length 52)
192.168.144.52.2824 > 192.168.252.253.443: Flags [S], cksum 0x9a89 (correct), seq 2251500828, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.013491 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59522 > 192.168.144.12.8090: Flags [S], cksum 0xb889 (incorrect -> 0x38a0), seq 3637235169, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 2468877893 ecr 0], length 0
00:00:00.547563 rule 66/0(match): pass in on em1: (tos 0x0, ttl 126, id 11221, offset 0, flags [DF], proto TCP (6), length 52)
192.168.254.113.63816 > 192.168.252.253.443: Flags [S], cksum 0x5292 (correct), seq 3594113936, win 64240, options [mss 1458,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.098009 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59523 > 192.168.144.90.443: Flags [S], cksum 0xb8d7 (incorrect -> 0xffee), seq 4203134005, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 2456182073 ecr 0], length 0
00:00:00.567528 rule 66/0(match): pass in on em1: (tos 0x0, ttl 126, id 11231, offset 0, flags [DF], proto TCP (6), length 52)
192.168.254.113.63817 > 192.168.252.253.443: Flags [S], cksum 0x2540 (correct), seq 4029671147, win 64240, options [mss 1458,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.199774 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59524 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x4919), seq 3844093588, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 1562502322 ecr 0], length 0
00:00:00.257451 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59525 > 192.168.144.90.443: Flags [S], cksum 0xb8d7 (incorrect -> 0xe466), seq 2928915251, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 4269040038 ecr 0], length 0
00:00:01.023924 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59526 > 192.168.144.90.443: Flags [S], cksum 0xb8d7 (incorrect -> 0x5cb8), seq 1989444906, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 2719525816 ecr 0], length 0
00:00:00.576284 rule 66/0(match): pass in on em1: (tos 0x0, ttl 126, id 52713, offset 0, flags [DF], proto TCP (6), length 52)
192.168.254.144.51516 > 192.168.252.253.443: Flags [S], cksum 0xabd5 (correct), seq 3962016833, win 64240, options [mss 1458,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.142410 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59527 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x9b69), seq 689108052, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 1328455328 ecr 0], length 0
00:00:00.317848 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59528 > 192.168.144.90.443: Flags [S], cksum 0xb8d7 (incorrect -> 0xab9f), seq 3510976964, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 1266392097 ecr 0], length 0
00:00:01.530653 rule 66/0(match): pass in on em1: (tos 0x0, ttl 126, id 52540, offset 0, flags [DF], proto TCP (6), length 52)
192.168.254.83.60378 > 192.168.252.253.443: Flags [S], cksum 0xe973 (correct), seq 2577565533, win 64240, options [mss 1319,nop,wscale 8,nop,nop,sackOK], length 0
00:00:00.199180 rule 60/0(match) [uid 80]: pass out on em0: (tos 0x0, ttl 64, id 0, offset 0, flags [DF], proto TCP (6), length 60)
192.168.144.253.59529 > 192.168.144.2.443: Flags [S], cksum 0xb87f (incorrect -> 0x482b), seq 2257932740, win 65228, options [mss 1460,nop,wscale 7,sackOK,TS val 4000356263 ecr 0], length 0
HA Proxy Config
global
uid 80
gid 80
chroot /var/haproxy
daemon
stats socket /var/run/haproxy.socket group proxy mode 775 level admin
nbproc 1
nbthread 4
hard-stop-after 60s
no strict-limits
maxconn 10000
tune.ssl.default-dh-param 4096
spread-checks 2
tune.bufsize 16384
tune.lua.maxmem 0
log /var/run/log audit debug
lua-prepend-path /tmp/haproxy/lua/?.lua
defaults
log global
option redispatch -1
maxconn 5000
timeout client 30s
timeout connect 30s
timeout server 30s
retries 3
default-server init-addr last,libc
# autogenerated entries for ACLs
# autogenerated entries for config in backends/frontends
# autogenerated entries for stats
# Frontend: LetsEncrypt_443 ()
frontend LetsEncrypt_443
bind 192.168.252.253:443 name 192.168.252.253:443 ssl prefer-client-ciphers ssl-min-ver TLSv1.2 ciphers ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES128-SHA256 ciphersuites TLS_AES_128_GCM_SHA256:TLS_AES_256_GCM_SHA384:TLS_CHACHA20_POLY1305_SHA256 crt-list /tmp/haproxy/ssl/605f6609f106d1.17683543.certlist
mode http
option http-keep-alive
default_backend acme_challenge_backend
option forwardfor
# tuning options
timeout client 30s
# logging options
# ACL: Nextcloud
acl acl_60604e669c3ca4.13013327 hdr(host) -i c.meyer.de
# ACTION: redirect_acme_challenges
use_backend acme_challenge_backend if acl_605f6d4b6453d2.03059920
# ACTION: Nextcloud
use_backend Nextcloud if acl_60604e669c3ca4.13013327
# Frontend: LetsEncrypt_80 ()
frontend LetsEncrypt_80
bind 192.168.252.253:80 name 192.168.252.253:80
mode tcp
default_backend acme_challenge_backend
# tuning options
timeout client 30s
# logging options
# ACL: find_acme_challenge
acl acl_605f6d4b6453d2.03059920 path_beg -i /.well-known/acme-challenge/
# ACTION: redirect_acme_challenges
use_backend acme_challenge_backend if acl_605f6d4b6453d2.03059920
# Frontend (DISABLED): 1_HTTP_frontend ()
# Frontend (DISABLED): 1_HTTPS_frontend ()
# Frontend (DISABLED): 0_SNI_frontend ()
# Backend: acme_challenge_backend (Added by Let's Encrypt plugin)
backend acme_challenge_backend
# health checking is DISABLED
mode http
balance source
# stickiness
stick-table type ip size 50k expire 30m
stick on src
# tuning options
timeout connect 30s
timeout server 30s
http-reuse safe
server acme_challenge_host 127.0.0.1:43580
# Backend: Nextcloud ()
backend Nextcloud
# health checking is DISABLED
mode http
balance source
# stickiness
stick-table type ip size 50k expire 30m
stick on src
# tuning options
timeout connect 30s
timeout server 30s
http-reuse safe
server Nextcloud2 192.168.144.90:11000 ssl verify none
server Nextcloud3 192.168.144.90:443 ssl verify none
server Nextcloud4 192.168.144.90:8443 ssl verify none
server Nextcloud5 192.168.144.90:8080 ssl verify none