Stack
- Nextcloud version:28.0.0.11
- Operating system and version: Ubuntu 22.04.3 LTS
- Apache or nginx version:2.4.52
- PHP version: with Zend OPcache v8.1.2-1ubuntu2.14
- MySQL: 8.0.35-0ubuntu0.22.04.1
The problem:
New install. No apps uploaded or added. Stock install via “latest.zip” in web directory. Everything working correctly. I am an experienced server admin (since 2005 on various systems), not an expert, but not new.
I did several installs of NextCloud recently, both through Snap and Manually in order to solve what ended up being some bad PHP settings. After solving that, I blew the install away and did a new install again which went as expected and everything went smoothly.
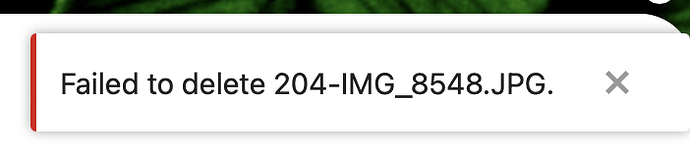
Now… I uploaded a test picture (yes, through the web interface), just to start tinkering with NextCloud. After uploading, I could not delete it. Yes, via the NextCloud interface (NOT via the command line or SFTP).
So then I tried to delete one of the included NextCloud files to see if that was also a problem and it is.
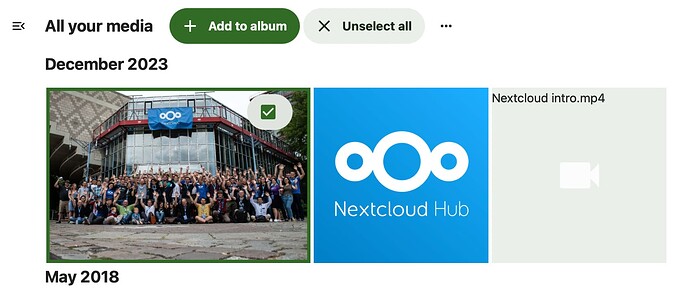
- Go to “All Media”
- Click the stock NextCloud image (the one with the people in front of a building) and try to delete.
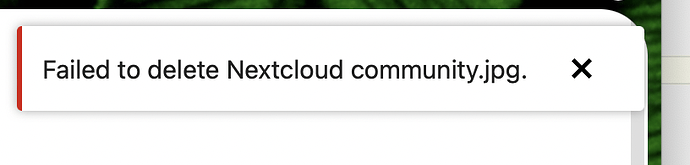
- Message: “Failed to delete Nextcloud community.jpg.
 ”
”
This also happens with any file, not just this one photo.
Permissions are correct in all directories and I have checked the file structure via occ.
I want to start using NextCloud, but I need to figure out why this is happening first. In searching the forums and web, I can see that this problem has popped up numerous times over the years. I am not doing anything non standard and there is no memcache in place at the moment.
I am open to exploring the stack and if any settings in PHP are causing this but to be clear, it is not working as it should.
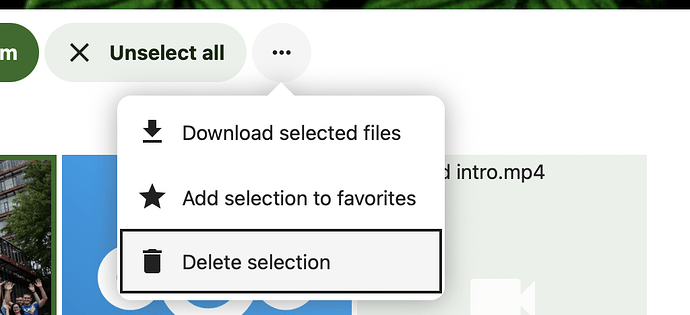
Here are some screen shots to better explain and demonstrate. I begin by checking the photo, then try to “Delete Selection” then I get the error message.