Hallo,
so bin jetzt einen Schritt weiter gekommen und möchte dies auch gerne teilen falls es jemand benötigt.
Grundlage der installation habe ich von dieser Seite
https://decatec.de/home-server/nextcloud-auf-ubuntu-server-20-04-lts-mit-nginx-mariadb-php-lets-encrypt-redis-und-fail2ban/comment-page-3/#comments
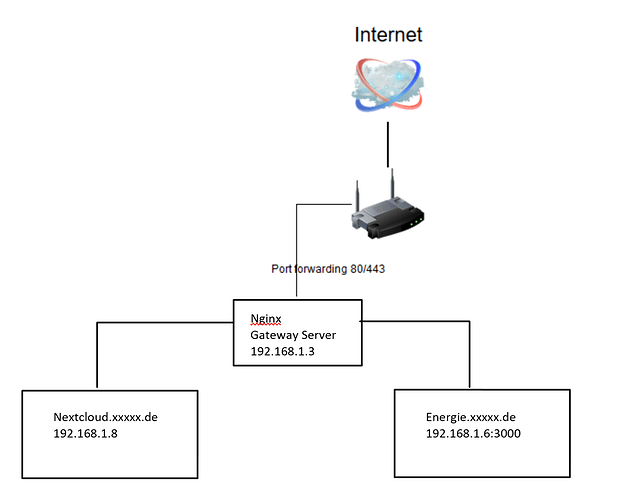
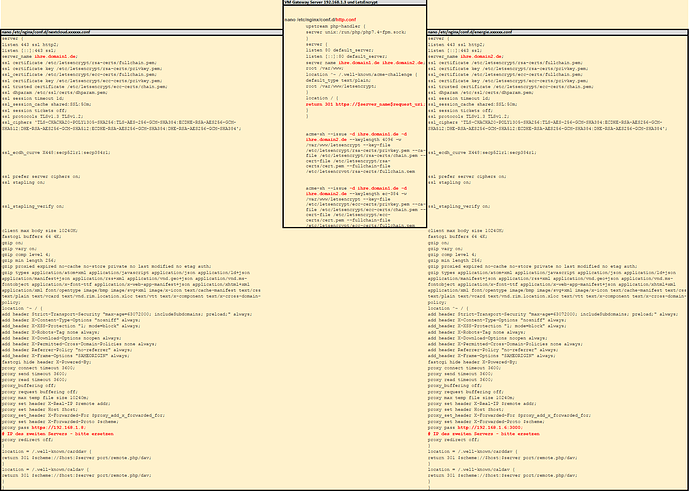
Auf dem Gateway Server habe ich 2 *.conf Dateien unter /etc/nginx/conf.d angelegt.
nextcloud.gateway.conf und die energie.gateway.conf. Ebenso sind dort die LetsEncrypht Zertifikate hinterlegt.
upstream php-handler {
server unix:/run/php/php7.4-fpm.sock;
}
server {
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name nextcloud.xxx.de;
location / {
proxy_pass http://192.168.x.x;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
add_header Cache-Control "public, max-age=15778463";
add_header Strict-Transport-Security "max-age=15768000; includeSubDomains; preload;" always;
add_header Referrer-Policy "no-referrer" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Download-Options "noopen" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header X-Robots-Tag "none" always;
add_header X-XSS-Protection "1; mode=block" always;
access_log off;
}
location = /.well-known/carddav {
return 301 $scheme://$host:$server_port/remote.php/dav;
}
location = /.well-known/caldav {
return 301 $scheme://$host:$server_port/remote.php/dav;
}
client_max_body_size 0;
; # SSL configuration
; # ECC certificates
ssl_certificate /etc/letsencrypt/nextcloud.xxx.de/ecc/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/nextcloud.xxx.de/ecc/key.pem;
; # This should be ca.pem (certificate with the additional intermediate certificate)
; # See here: https://certbot.eff.org/docs/using.html
; # ECC
ssl_trusted_certificate /etc/letsencrypt/nextcloud.xxx.de/ecc/ca.pem;
; # RSA certificates
ssl_certificate /etc/letsencrypt/nextcloud.xxx.de/rsa/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/nextcloud.xxx.de/rsa/key.pem;
; # Include headers and SSL specific stuff.
include /etc/nginx/snippets/ssl.conf;
include /etc/nginx/snippets/headers.conf;
;# root /var/www/nextcloud/;
}
server {
if ($host = nextcloud.xxx.de) {
return 301 https://$host$request_uri;
} # managed by Certbot
listen 80;
server_name nextcloud.xxx.de;
return 404; # managed by Certbot
}
und für meinen energie VM-Server
die energie.gateway.conf im gleichen Verzeichnis
server {
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name energie.xxx.de;
location / {
proxy_pass http://192.168.x.x:3000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
client_max_body_size 0;
;# SSL configuration
;# ECC certificates
ssl_certificate /etc/letsencrypt/energie.xxx.de/ecc/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/energie.xxx.de/ecc/key.pem;
;# This should be ca.pem (certificate with the additional intermediate certificate)
;# See here: https://certbot.eff.org/docs/using.html
;# ECC
ssl_trusted_certificate /etc/letsencrypt/energie.xxx.de/ecc/ca.pem;
;# RSA certificates
ssl_certificate /etc/letsencrypt/energie.xxx.de/rsa/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/energie.xxx.de/rsa/key.pem;
;# Include headers and SSL specific stuff.
include /etc/nginx/snippets/ssl.conf;
include /etc/nginx/snippets/headers.conf;
}
server {
if ($host = energie.xxx.de) {
return 301 https://$host$request_uri;
} # managed by Certbot
listen 80;
server_name energie.xxx.de;
return 404; # managed by Certbot
}
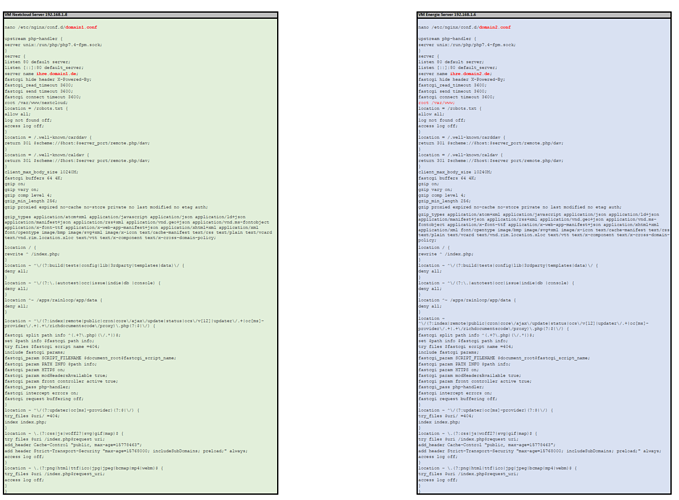
auf dem Nextcloud Server liegt unter /etc/nginx/conf.d die nextcloud.xxx.conf mit folgendem Inhalt.
upstream php-handler {
server unix:/run/php/php7.4-fpm.sock;
}
server {
;# listen 80 http2;
;# listen [::]:443 ssl http2;
listen 80 default_server;
listen [::]:80 default_server;
server_name nextcloud.rweckenmann.de;
; # SSL configuration
; # RSA certificates
;# ssl_certificate /etc/letsencrypt/nextcloud.meinedomain.de/rsa/fullchain.pem;
;# ssl_certificate_key /etc/letsencrypt/nextcloud.meinedomain.de/rsa/key.pem;
ECC certificates
;# ssl_certificate /etc/letsencrypt/nextcloud.meinedomain.de/ecc/fullchain.pem;
;# ssl_certificate_key /etc/letsencrypt/nextcloud.meinedomain.de/ecc/key.pem;
; # This should be ca.pem (certificate with the additional intermediate certificate)
; # See here: https://certbot.eff.org/docs/using.html
; # ECC
;# ssl_trusted_certificate /etc/letsencrypt/nextcloud.meinedomain.de/ecc/ca.pem;
; # Include SSL configuration
;# include /etc/nginx/snippets/ssl.conf;
;# Include headers
include /etc/nginx/snippets/headers.conf;
;#
;# Nextcloud configuration
;#
;# Path to the root of your installation
root /var/www/nextcloud/;
location = /robots.txt {
allow all;
log_not_found off;
access_log off;
}
;# The following 2 rules are only needed for the user_webfinger app. Uncomment it if you’re planning to use this app.
#rewrite ^/.well-known/host-meta /public.php?service=host-meta last;
#rewrite ^/.well-known/host-meta.json /public.php?service=host-meta-json last;
;# Well-known URL for CardDAV
location = /.well-known/carddav {
return 301 $scheme://$host/remote.php/dav;
}
;# Well-known URL for CalDAV
location = /.well-known/caldav {
return 301 $scheme://$host/remote.php/dav;
}
;# Well-known URL for Webfinger
;# Regardless of this rule, you’ll get a warning in the admin UI when the social app is not installed
location = /.well-known/webfinger {
return 301 $scheme://$host/public.php?service=webfinger;
}
;# set max upload size
client_max_body_size 10G;
fastcgi_buffers 64 4K;
;# Enable gzip but do not remove ETag headers
gzip on;
gzip_vary on;
gzip_comp_level 4;
gzip_min_length 256;
gzip_proxied expired no-cache no-store private no_last_modified no_etag auth;
gzip_types application/atom+xml application/javascript application/json application/ld+json application/manifest+json application/rss+xml application/vnd.geo+json application/vnd.ms-fontobject application/x-font-ttf application/x-web-app-manifest+json application/xhtml+xml application/xml font/opentype image/bmp image/svg+xml image/x-icon text/cache-manifest text/css text/plain text/vcard text/vnd.rim.location.xloc text/vtt text/x-component text/x-cross-domain-policy;
;# Uncoment if your server is build with the ngx_pagespeed module This module is currently not supported.
#pagespeed off;
location / {
rewrite ^ /index.php;
}
location ~ ^/(?:build|tests|config|lib|3rdparty|templates|data)/ {
deny all;
}
location ~ ^/(?:.|autotest|occ|issue|indie|db_|console) {
deny all;
}
location ~ ^/(?:index|remote|public|cron|core/ajax/update|status|ocs/v[12]|updater/.+|oc[ms]-provider/.+).php(?:$|/) {
fastcgi_split_path_info ^(.+?.php)(/.*|)$;
set $path_info $fastcgi_path_info;
try_files $fastcgi_script_name =404;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name;
fastcgi_param PATH_INFO $fastcgi_path_info;
fastcgi_param HTTPS on;
#Avoid sending the security headers twice
fastcgi_param modHeadersAvailable true;
fastcgi_param front_controller_active true;
fastcgi_pass php-handler;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
fastcgi_read_timeout 600;
fastcgi_send_timeout 600;
fastcgi_connect_timeout 600;
fastcgi_param PHP_VALUE "upload_max_filesize = 10G
post_max_size = 10G
max_execution_time = 3600
output_buffering = off";
}
location ~ ^/(?:updater|ocs-provider|ocm-provider)(?:$|/) {
try_files $uri/ =404;
index index.php;
}
;# Adding the cache control header for js and css files
;# Make sure it is BELOW the PHP block
location ~ .(?:css|js|woff2?|svg|gif)$ {
try_files $uri /index.php$request_uri;
add_header Cache-Control “public, max-age=15778463”;
# Add headers to serve security related headers (It is intended to
# have those duplicated to the ones above)
# Before enabling Strict-Transport-Security headers please read into
# this topic first.
add_header Strict-Transport-Security “max-age=63072000; includeSubdomains; preload;” always;
# WARNING: Only add the preload option once you read about
# the consequences in https://hstspreload.org/. This option
# will add the domain to a hardcoded list that is shipped
# in all major browsers and getting removed from this list
# could take several months
add_header X-Content-Type-Options "nosniff" always;
add_header X-XSS-Protection "1; mode=block" always;
add_header X-Robots-Tag "none" always;
add_header X-Download-Options "noopen" always;
add_header X-Frame-Options "SAMEORIGIN" always;
add_header X-Permitted-Cross-Domain-Policies "none" always;
add_header Referrer-Policy "no-referrer" always;
# Optional: Don't log access to assets
access_log off;
}
location ~ .(?:png|html|ttf|ico|jpg|jpeg)$ {
try_files $uri /index.php$request_uri;
# Optional: Don’t log access to other assets
access_log off;
}
}
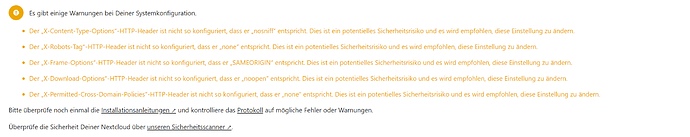
Mit dieser Konfiguration funktioniert soweit alles bis auf die folgenden Fehler Meldungen in der Nextcloud
die Einträge sind doch vorhanden warum meckert er hier?
Kann mir jemand weiterhelfen?
Gruß
Ralf