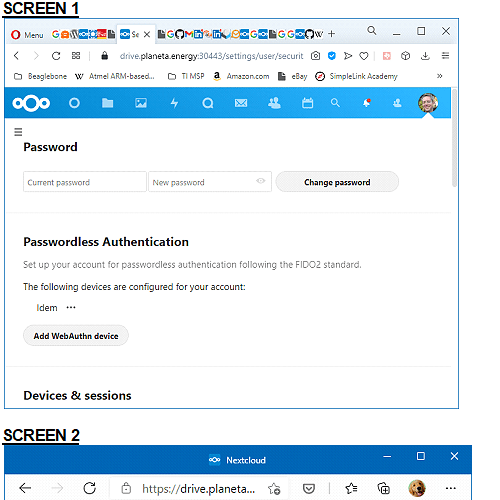
Hi, I have Nextcloud up and running and have configured a Fido2 key for WebAuthn access.
Now I’d like to require the use of the key for login.
I tried Settings/Security/Two-Factor Authentication/Enforce 2-factor authentication.
But that doesn’t work. You are still presented with a Username/password screen for login. That’s not the end of the world - you can still click “Log in with a device”.
But when you do that - plug in the device and touch it, fine - But then you get a dialog “Two-factor authentication is enforced, but has not been configured for your account.”
Now we are well and truly locked out. Fortunately I still was logged in in another window and could revert the setting.
So I guess “two-factor authentication” and “WebAuthn” are two different things.
It appears that “Enforce 2-factor authentication” is not the answer.
How can I require the user to “Log in with a device”?
Thanks,
Brad