TASK [prep_nextcloud : install nextcloud] ************************************************************************************************************************
Sunday 21 October 2018 08:08:30 +0000 (0:00:00.102) 0:02:38.753 ********
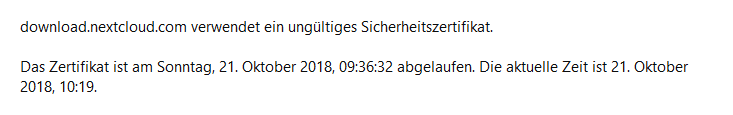
fatal: [localhost]: FAILED! => {“changed”: false, “msg”: “Failed to validate the SSL certificate for download.nextcloud.com:443. Make sure your managed systems have a valid CA certificate installed. You can use validate_certs=False if you do not need to confirm the servers identity but this is unsafe and not recommended. Paths checked for this platform: /etc/ssl/certs, /etc/pki/ca-trust/extracted/pem, /etc/pki/tls/certs, /usr/share/ca-certificates/cacert.org, /etc/ansible. The exception msg was: [SSL: CERTIFICATE_VERIFY_FAILED] certificate verify failed (_ssl.c:726).”}
Hallo, bin leider in die selbe Falle gelaufen. Wann wird das Zertifikat auf dem Server erneuert???
Das kann doch nicht so schwer sein.
I am not able to update either. Similar issue happened already: Ssl certificate expired of "https://download.nextcloud.com"
It looks like a better solution has not been implemented yet.
wget has an option --no-check-certificate. i guess curl as well.
but you have to hope that download.nextcloud.com is the correct server. 
It won’t fix automatic update through the web page though…
this is a workaround for own hosted instances, but the web-auto-updater for hosters without access to the cli or own linux can not influence this.
It can’t be difficult to renew the certificate in time.
if it’s a letsencrypt certificate it should auto-update. unless something went wrong. certbot crashed. or something like that.
nevertheless we have sunday morning and i guess no one is in office. 
@jospoortvliet monitoring certbot and certificates on download.nextcloud.com would be a god idea.
I’m with you on this. Then I wait until Monday.
It actually IS a Let’sEncrypt certificate, which obviously has not been renewed in time. Let’sEncrypt certificates are valid for 30 days and are normally renewed after 20 days, so something like this just should not happen until noone monitored the error messages from the updater script (certbot, dehydrated or similar).
However I have to admit this has already happened to me as well, but only on an internal server - I didn’t notice that cron just skipped my updater script as it didn’t follow the naming conventions… (It included a dot in the filename.)
now the bug has been fixed
So yeah, certbot crashed. Again. It seems to have done that for EVERY time it had to update the certs for the last… I dunno, 5 renewals. Morris has wiped the setup and created a new one, fingers crossed for the next renewal… Sigh ![]()
![]()